AutoPhish vs Decode This Text
Side-by-side comparison to help you choose the right tool.
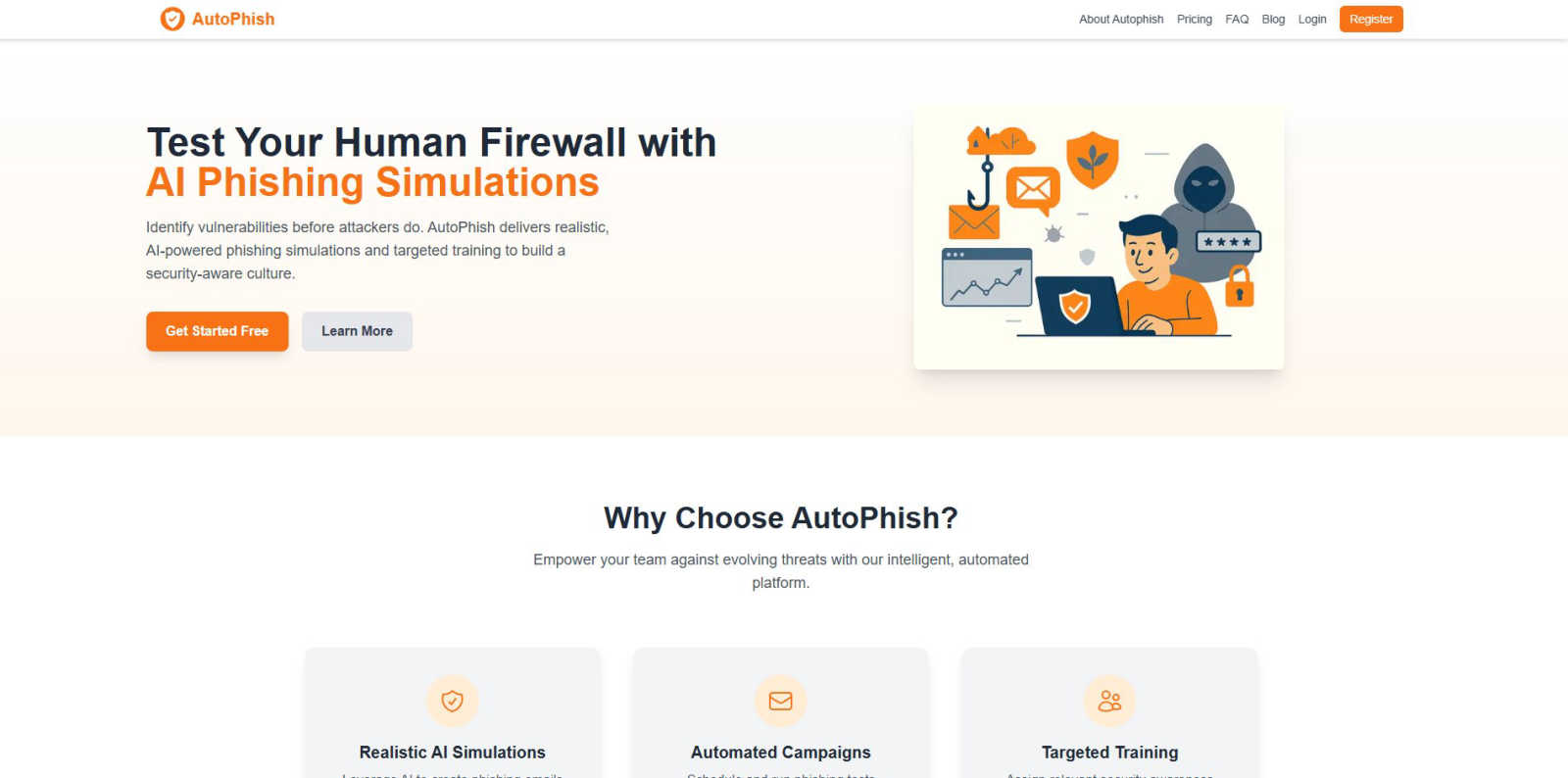
AutoPhish uses AI to run automated phishing simulations and deliver targeted security training.
Last updated: March 1, 2026
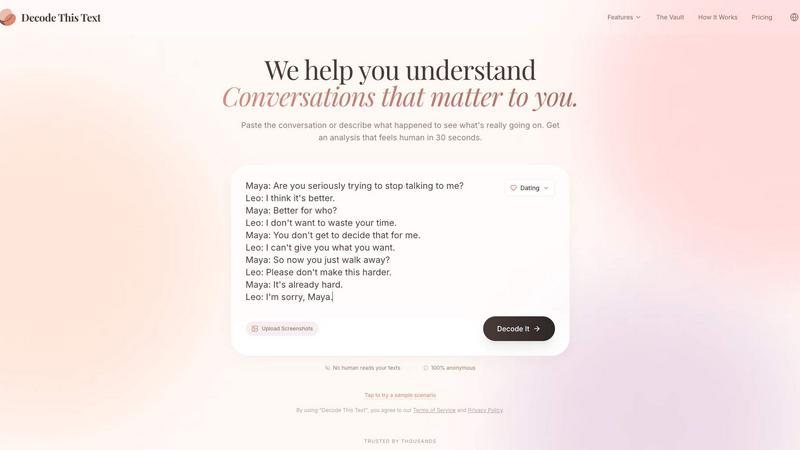
Decode This Text
Decode This Text provides instant, human-like analysis of confusing conversations in just 30 seconds.
Last updated: February 28, 2026
Visual Comparison
AutoPhish
Decode This Text
Feature Comparison
AutoPhish
AI-Powered Phishing Simulation Engine
The platform's core engine utilizes artificial intelligence to dynamically generate and adapt phishing email templates. This AI analyzes current threat intelligence and real-world attack patterns to create simulations that accurately mimic the latest tactics, techniques, and procedures (TTPs) used by malicious actors. The content is context-aware, allowing for customization based on industry, department, or specific known threats, ensuring a realistic and challenging test of employee awareness beyond generic, easily recognizable templates.
Automated Campaign Management
AutoPhish provides full automation for the phishing simulation lifecycle. Administrators can schedule campaigns in advance, define target user groups, and set launch parameters. The platform handles the entire execution process, including email delivery, click and interaction tracking, and post-campaign reporting. This automation ensures consistent, ongoing testing without requiring manual intervention from security teams, saving significant time and operational overhead while maintaining program regularity.
Granular Reporting and Analytics
Following each simulation campaign, the platform delivers detailed, actionable analytics. Reports provide metrics on click-through rates, credential submission attempts, and user susceptibility across different departments or roles. Data is presented in dashboards that highlight high-risk individuals and trends over time. This granular visibility allows security teams to quantitatively measure the human risk surface and track the effectiveness of their awareness training initiatives with precision.
Targeted, Automated Training Assignment
Based on simulation results, AutoPhish automatically assigns relevant security awareness training modules to users. This targeted approach ensures that individuals who fail a simulation receive immediate, context-specific education on the phishing tactics they encountered. Training assignments can also be role-based, providing finance teams with different content than engineering staff, for example. This closed-loop system of test, measure, and educate accelerates the development of a security-conscious workforce.
Decode This Text
Screenshot Upload & OCR Processing
This feature allows users to bypass manual text entry by directly uploading a photograph or screenshot of their chat conversation. The system employs Optical Character Recognition (OCR) technology to automatically extract and digitize all textual content from the image for analysis. This streamlines the input process, ensures accuracy in capturing the exact wording and formatting, and is particularly useful for analyzing long or complex message threads that would be cumbersome to copy and paste manually.
Multi-Dimensional Tone Analysis
The platform performs a granular, multi-faceted analysis of the emotional tone embedded within a message. It goes beyond simple sentiment to measure specific tonal qualities such as warmth, formality, sarcasm, or indifference. This analysis is presented through quantified metrics (e.g., Tone: 75%), providing an objective assessment of the emotional temperature. This technical breakdown helps users avoid personal bias in interpreting whether a sender is being friendly, passive-aggressive, genuinely busy, or emotionally distant.
Behavioral Pattern Detection
This advanced feature scans conversation history and contextual clues to identify recurring behavioral patterns that may not be immediately apparent. The algorithm analyzes factors like timing of messages (e.g., consistently late-night contact), response latency, avoidance of specific questions, and changes in message length or engagement level. By detecting these patterns, the tool provides insights into potential underlying motivations or shifts in interest, offering a longitudinal view of the communication dynamic.
AI-Generated Response Recommendations
Upon completing its analysis, the tool generates three contextually appropriate response options tailored to the user's desired communication style. These typically include a calm/neutral response, a direct/inquisitive response, and a firm/boundary-setting response. Each recommendation is crafted to align with the analyzed intent and tone of the original message, providing users with a strategic toolkit to reply with confidence and tactical awareness, thereby optimizing the outcome of the interaction.
Use Cases
AutoPhish
Proactive Human Risk Assessment
Organizations use AutoPhish to conduct regular, controlled phishing simulations across their entire employee base. This proactive testing identifies which users are most susceptible to social engineering attacks, quantifying the human element of security risk. The data gathered provides a baseline security posture metric and helps prioritize security awareness efforts and budget allocation towards the most vulnerable segments of the workforce.
Compliance and Audit Readiness
For companies subject to regulatory frameworks like GDPR, HIPAA, or ISO 27001, AutoPhish provides documented evidence of ongoing security awareness training and testing. The platform's detailed reporting and audit trails demonstrate due diligence in educating employees about phishing threats, which is a common requirement for compliance. This helps organizations pass security audits and meet regulatory mandates for employee cybersecurity training.
Security Awareness Program Automation
IT and security teams leverage AutoPhish to automate the repetitive tasks associated with running a security awareness program. Instead of manually creating emails, sending tests, and tracking responses, the platform handles these operations. This allows security professionals to focus on analyzing results, developing strategic improvements, and responding to actual security incidents rather than administrative program management.
Post-Incident Reinforcement Training
Following a real phishing incident or a failed simulation where multiple users clicked a malicious link, AutoPhish enables rapid deployment of targeted training. Administrators can immediately assign specific training modules related to the attack vector used, reinforcing correct behavior and ensuring employees understand the specific red flags they missed. This timely intervention strengthens institutional memory and reduces the likelihood of repeat failures.
Decode This Text
Analyzing Romantic Interest & Dating App Conversations
Users can paste exchanges from dating apps or text conversations with potential romantic partners to decode mixed signals. The tool analyzes messages like "I'll let you know" or sudden drops in communication frequency to determine genuine interest level versus polite disengagement. It provides clarity on whether a person is truly busy, losing interest, or employing avoidant communication tactics, empowering the user to respond appropriately rather than over-investing or misreading the situation.
Interpreting Ambiguous Workplace Communication
This use case involves deciphering cryptic emails, brief Slack messages, or vague feedback from managers and colleagues. For example, analyzing a one-word email from a boss to assess if it signifies anger, simple acknowledgment, or haste. The tool evaluates professional tone, intent, and potential subtext, helping users understand the true meaning behind phrases like "we'll keep your resume on file" or a suddenly silent group chat after a contribution, enabling more effective and politically savvy professional responses.
Navigating Complex Family & Friend Dynamics
The platform assists in understanding sensitive communications within personal networks. This includes analyzing why a family group chat went silent after a specific message, interpreting a friend's increasingly short replies, or determining the emotional subtext behind a sibling's vague text. By providing an objective "reality check," it helps users navigate emotional undercurrents, perceived slights, and social tensions with greater empathy and clarity, reducing personal conflict and misunderstanding.
Preventing Regretful Communication Sent Prematurely
A critical use case is utilizing the tool as a final review layer before sending an emotionally charged or high-stakes message. Users can input their drafted response to a provocative text, email, or social media comment. The tool will analyze the draft's tone, predict its likely reception, and suggest calmer, more effective alternatives. This serves as a preventative measure against sending messages fueled by frustration that could damage relationships or professional reputations.
Overview
About AutoPhish
AutoPhish is an advanced, AI-powered cybersecurity platform engineered to proactively strengthen an organization's human firewall through realistic phishing simulations and targeted security awareness training. The platform is designed for IT security teams, compliance officers, and organizational leaders across all industries who are responsible for mitigating the risk posed by social engineering attacks. Its core value proposition lies in its ability to leverage artificial intelligence to generate highly convincing, context-aware phishing email templates that mimic current, real-world threat actor tactics, techniques, and procedures (TTPs). This moves beyond generic simulations to provide a true test of employee vigilance. The platform automates the entire lifecycle of a security awareness program, from campaign scheduling and execution to detailed analytics and the automated assignment of role-specific training modules based on individual user performance. By identifying behavioral vulnerabilities before malicious actors can exploit them, AutoPhish enables organizations to cultivate a resilient, security-aware culture, reduce incident response costs, and demonstrably improve their overall security posture against evolving email-based threats.
About Decode This Text
Decode This Text is a sophisticated AI-powered communication analysis platform engineered to provide users with precise, data-driven insights into the subtext of digital conversations. The tool functions as an analytical engine, processing user-provided text, chat screenshots, or contextual descriptions to deliver a comprehensive breakdown of a message's underlying intent, emotional tone, and behavioral patterns. It is designed for individuals seeking to eliminate ambiguity in personal, professional, and social communications, thereby enhancing interpersonal effectiveness and reducing relational anxiety. The core value proposition lies in its ability to transform subjective interpretation into objective analysis within a 30-second processing window. The platform operates with a strict privacy protocol where no human ever reviews the submitted content, ensuring 100% anonymity. Target users include professionals navigating complex workplace correspondence, individuals deciphering romantic or social cues, and anyone aiming to improve their communicative clarity and response strategy without relying on biased external opinions.
Frequently Asked Questions
AutoPhish FAQ
How does AutoPhish ensure simulation emails are safe?
AutoPhish simulations are conducted in a fully controlled environment. All links within simulation emails point to internal, secure servers owned and operated by AutoPhish, not to external malicious websites. No actual malware is deployed, and any credentials entered by users during a test are captured in a secure, encrypted database solely for reporting purposes and are never used for authentication. The platform is designed to educate, not harm, user systems or data.
What is required to start sending phishing simulations?
To begin, an administrator must verify ownership of the company domain they intend to use for sending simulations. This involves configuring specific DNS records (like SPF) to authorize AutoPhish to send email on the organization's behalf, ensuring deliverability and preventing the simulations from being marked as spam. The platform provides step-by-step guidance for this domain verification and connection process.
Can I customize the phishing templates?
Yes, AutoPhish offers extensive customization capabilities. While the AI engine provides a library of realistic, up-to-date templates, administrators can fully edit email subject lines, body content, sender addresses (from verified domains), and landing pages. This allows for the creation of hyper-targeted simulations that reflect internal communication styles or mimic specific, credible threats relevant to the organization.
How does the targeted training work?
When a user interacts with a simulated phishing email (e.g., clicks a link), AutoPhish logs this event. The platform can be configured to automatically enroll that user in a pre-defined training course relevant to the type of phishing attack simulated. Training modules are typically short, interactive videos or quizzes focused on identifying phishing indicators. Assignment rules can also be based on user department or job role for broader, proactive education.
Decode This Text FAQ
How does Decode This Text ensure my privacy and anonymity?
Decode This Text operates on a strict no-human-review policy. All text analysis is performed entirely by automated AI algorithms. Submitted conversations, whether pasted text or uploaded screenshots, are processed without being stored or viewed by any human employee. The service is designed to be 100% anonymous, requiring no personal identification for use, ensuring your private communications remain confidential.
What is the difference between this tool and asking a friend for advice?
Unlike human friends who bring their own biases, emotional baggage, and limited perspectives, Decode This Text provides a consistent, objective, and data-driven analysis. It focuses solely on the textual and contextual evidence provided, ignoring external drama. It offers immediate availability, eliminates the social risk of over-sharing, and delivers reproducible analysis based on linguistic and behavioral patterns rather than subjective opinion.
Can the tool analyze messages in languages other than English?
The primary operational language as indicated by the provided content is Spanish, with the interface and analysis built for Spanish-language text. The technical specifications regarding additional language support are not explicitly detailed in the provided context. For accurate analysis, users should consult the platform's official documentation or support channels for the current list of supported languages and their respective processing capabilities.
What kind of input does the system accept for analysis?
The platform accepts three primary input modalities: 1) Direct text paste, where users copy and paste the message thread into a designated field. 2) Screenshot upload, utilizing OCR to extract text from an image of the conversation. 3) Contextual description, where users can narratively describe the situation and the communication in question. The system is engineered to parse and derive insights from all these structured and unstructured data formats.
Alternatives
AutoPhish Alternatives
AutoPhish is an AI-powered cybersecurity platform within the business intelligence and productivity management category. It specializes in automating sophisticated phishing simulations and targeted security awareness training to proactively strengthen an organization's human layer of defense. Organizations may seek alternatives to AutoPhish for various operational and strategic reasons. Common drivers include budget constraints and specific pricing model requirements, the need for different feature integrations or platform capabilities, and preferences for alternative deployment methods or user interface designs. When evaluating alternative solutions, key criteria should include the sophistication and realism of the simulation engine, the depth of analytics and reporting provided, the flexibility and automation of campaign management, and the relevance and personalization of the accompanying training modules. The chosen platform must align with both technical requirements and organizational security culture goals.
Decode This Text Alternatives
Decode This Text is a productivity and management tool designed to analyze and interpret ambiguous or confusing text-based communications. It provides users with rapid, human-like analysis of messages, delivering insights into underlying intentions, emotional tone, and suggested responses within a 30-second timeframe. Users may seek alternatives for various practical reasons. Common motivations include budget constraints, where the pricing model of a primary tool may not align with individual or organizational needs. Others may require specific feature sets not offered, such as integration with particular platforms, support for different communication channels, or more advanced analytical capabilities. Platform compatibility, including mobile app availability or browser extension support, is another frequent consideration. When evaluating an alternative solution, key criteria should include the core analytical engine's accuracy and depth, the range of supported input formats, and the speed of the analysis. Security and data privacy protocols are paramount, as sensitive communications are being processed. Additionally, the flexibility of the response framework and the tool's ability to provide actionable, context-aware advice should be assessed to ensure it meets the user's specific communication enhancement goals.

