Decode This Text vs securememo.app
Side-by-side comparison to help you choose the right tool.
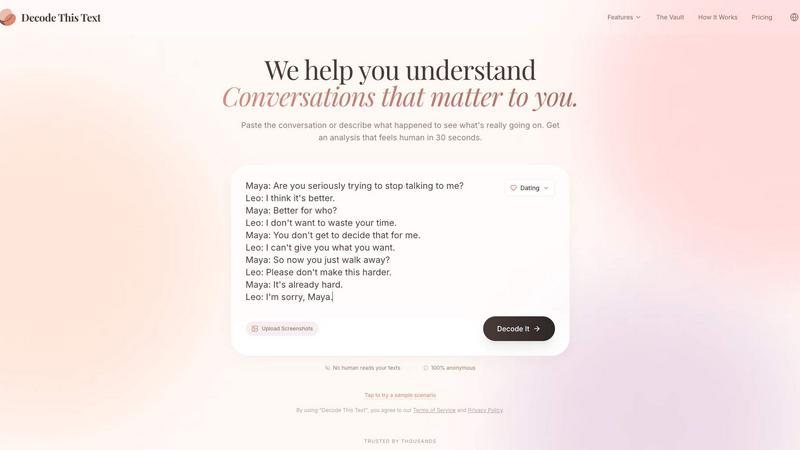
Decode This Text
Decode This Text provides instant, human-like analysis of confusing conversations in just 30 seconds.
Last updated: February 28, 2026

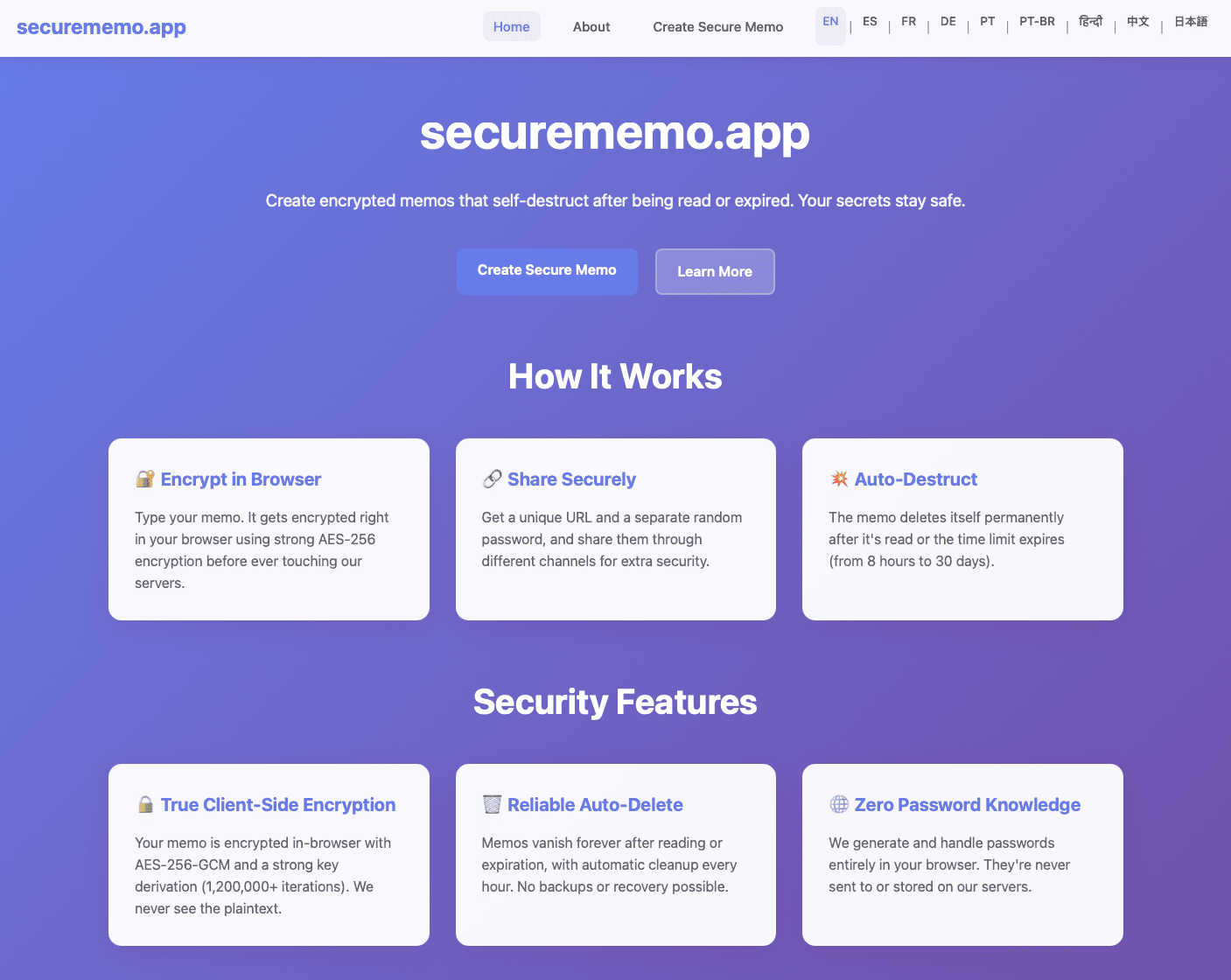
securememo.app
Securememo.app is an open source, client side encrypted memo service with zero tracking.
Visual Comparison
Decode This Text
securememo.app
Feature Comparison
Decode This Text
Screenshot Upload & OCR Processing
This feature allows users to bypass manual text entry by directly uploading a photograph or screenshot of their chat conversation. The system employs Optical Character Recognition (OCR) technology to automatically extract and digitize all textual content from the image for analysis. This streamlines the input process, ensures accuracy in capturing the exact wording and formatting, and is particularly useful for analyzing long or complex message threads that would be cumbersome to copy and paste manually.
Multi-Dimensional Tone Analysis
The platform performs a granular, multi-faceted analysis of the emotional tone embedded within a message. It goes beyond simple sentiment to measure specific tonal qualities such as warmth, formality, sarcasm, or indifference. This analysis is presented through quantified metrics (e.g., Tone: 75%), providing an objective assessment of the emotional temperature. This technical breakdown helps users avoid personal bias in interpreting whether a sender is being friendly, passive-aggressive, genuinely busy, or emotionally distant.
Behavioral Pattern Detection
This advanced feature scans conversation history and contextual clues to identify recurring behavioral patterns that may not be immediately apparent. The algorithm analyzes factors like timing of messages (e.g., consistently late-night contact), response latency, avoidance of specific questions, and changes in message length or engagement level. By detecting these patterns, the tool provides insights into potential underlying motivations or shifts in interest, offering a longitudinal view of the communication dynamic.
AI-Generated Response Recommendations
Upon completing its analysis, the tool generates three contextually appropriate response options tailored to the user's desired communication style. These typically include a calm/neutral response, a direct/inquisitive response, and a firm/boundary-setting response. Each recommendation is crafted to align with the analyzed intent and tone of the original message, providing users with a strategic toolkit to reply with confidence and tactical awareness, thereby optimizing the outcome of the interaction.
securememo.app
Client-Side Encryption
All data processing and encryption occur exclusively within the user's web browser using robust cryptographic algorithms before any data is sent to the securememo.app servers. This architectural design ensures that plaintext content of memos is never exposed to the network or the service's infrastructure. The encryption keys are generated and managed locally, guaranteeing that only the intended recipient with the correct password can ever decrypt and view the note's contents, providing a true zero-knowledge environment.
Self-Destructing Notes
Each memo created on the platform is ephemeral by design. Once a note is created and a unique link is generated, it is programmed to automatically and permanently delete itself from the servers after being accessed by the recipient. This feature enforces data minimalism and eliminates the risk of sensitive information persisting in any database, providing a secure, one-time viewing mechanism that leaves no long-term digital footprint.
Zero-Knowledge Password Generation
For each memo, a strong, cryptographically random password is generated locally on the creator's device. This password is never transmitted to or stored by securememo.app's servers. The service operates on a zero-knowledge principle where it has no access to this decryption key. Secure sharing of the memo requires the creator to transmit this password to the recipient through a separate, trusted channel (e.g., a secure messaging app or in person), creating a necessary two-factor access mechanism.
No-Account Anonymity
The service is designed for immediate use without any registration, sign-up, or account creation process. This approach maximizes user privacy and anonymity by not collecting any personally identifiable information (PII) such as email addresses or usernames. Users can create and share encrypted memos instantly, which lowers the barrier to entry and aligns with the product's core philosophy of privacy-by-design and operational security.
Use Cases
Decode This Text
Analyzing Romantic Interest & Dating App Conversations
Users can paste exchanges from dating apps or text conversations with potential romantic partners to decode mixed signals. The tool analyzes messages like "I'll let you know" or sudden drops in communication frequency to determine genuine interest level versus polite disengagement. It provides clarity on whether a person is truly busy, losing interest, or employing avoidant communication tactics, empowering the user to respond appropriately rather than over-investing or misreading the situation.
Interpreting Ambiguous Workplace Communication
This use case involves deciphering cryptic emails, brief Slack messages, or vague feedback from managers and colleagues. For example, analyzing a one-word email from a boss to assess if it signifies anger, simple acknowledgment, or haste. The tool evaluates professional tone, intent, and potential subtext, helping users understand the true meaning behind phrases like "we'll keep your resume on file" or a suddenly silent group chat after a contribution, enabling more effective and politically savvy professional responses.
Navigating Complex Family & Friend Dynamics
The platform assists in understanding sensitive communications within personal networks. This includes analyzing why a family group chat went silent after a specific message, interpreting a friend's increasingly short replies, or determining the emotional subtext behind a sibling's vague text. By providing an objective "reality check," it helps users navigate emotional undercurrents, perceived slights, and social tensions with greater empathy and clarity, reducing personal conflict and misunderstanding.
Preventing Regretful Communication Sent Prematurely
A critical use case is utilizing the tool as a final review layer before sending an emotionally charged or high-stakes message. Users can input their drafted response to a provocative text, email, or social media comment. The tool will analyze the draft's tone, predict its likely reception, and suggest calmer, more effective alternatives. This serves as a preventative measure against sending messages fueled by frustration that could damage relationships or professional reputations.
securememo.app
Secure Credential Sharing
Professionals can safely transmit sensitive login credentials, API keys, or database passwords to colleagues or clients. By using securememo.app, the credentials are encrypted end-to-end and self-destruct upon first view, mitigating the risks associated with sending such data via email, SMS, or standard messaging platforms where logs are retained and security may be compromised.
Confidential Legal or Business Communication
Lawyers, journalists, or business executives can share confidential case details, draft documents, or strategic information with the assurance of client-side encryption and ephemeral storage. This use case is critical for maintaining attorney-client privilege or protecting sensitive business intelligence from interception or unauthorized server-side access.
One-Time Private Messaging
Individuals requiring a private, non-traceable conversation channel can use the service to exchange messages that leave no permanent record. This is applicable for whistleblowers, individuals in sensitive situations, or anyone needing to share personal information without creating a persistent chat history that could be subpoenaed or hacked.
Secure Disposable Notes for Personal Data
Users can create encrypted notes containing personal information like social security numbers, bank account details, or travel documents for their own temporary reference. The self-destruct feature acts as a secure, automated cleanup, ensuring this highly sensitive data does not remain stored on any device or cloud service indefinitely.
Overview
About Decode This Text
Decode This Text is a sophisticated AI-powered communication analysis platform engineered to provide users with precise, data-driven insights into the subtext of digital conversations. The tool functions as an analytical engine, processing user-provided text, chat screenshots, or contextual descriptions to deliver a comprehensive breakdown of a message's underlying intent, emotional tone, and behavioral patterns. It is designed for individuals seeking to eliminate ambiguity in personal, professional, and social communications, thereby enhancing interpersonal effectiveness and reducing relational anxiety. The core value proposition lies in its ability to transform subjective interpretation into objective analysis within a 30-second processing window. The platform operates with a strict privacy protocol where no human ever reviews the submitted content, ensuring 100% anonymity. Target users include professionals navigating complex workplace correspondence, individuals deciphering romantic or social cues, and anyone aiming to improve their communicative clarity and response strategy without relying on biased external opinions.
About securememo.app
Securememo.app is a specialized web application engineered for the secure creation and transmission of sensitive textual information. It functions as a privacy-first, ephemeral note-taking and sharing service that operates entirely within a user's web browser. The core value proposition is its uncompromising commitment to data sovereignty and user anonymity through a robust implementation of client-side encryption and a zero-knowledge architecture. This means all cryptographic operations, including key generation and data encryption/decryption, are performed locally on the user's device before any data is transmitted. The service is designed for individuals and professionals who require a trusted, temporary channel for sharing confidential data such as passwords, access keys, personal messages, or sensitive documents in plain text. By eliminating the need for user accounts and ensuring the service provider has no technical means to access the content of the memos, securememo.app prioritizes ease of use without sacrificing the highest standards of security. Its availability in over 20 languages further extends its accessibility to a global audience seeking a reliable tool for discrete, one-time communication.
Frequently Asked Questions
Decode This Text FAQ
How does Decode This Text ensure my privacy and anonymity?
Decode This Text operates on a strict no-human-review policy. All text analysis is performed entirely by automated AI algorithms. Submitted conversations, whether pasted text or uploaded screenshots, are processed without being stored or viewed by any human employee. The service is designed to be 100% anonymous, requiring no personal identification for use, ensuring your private communications remain confidential.
What is the difference between this tool and asking a friend for advice?
Unlike human friends who bring their own biases, emotional baggage, and limited perspectives, Decode This Text provides a consistent, objective, and data-driven analysis. It focuses solely on the textual and contextual evidence provided, ignoring external drama. It offers immediate availability, eliminates the social risk of over-sharing, and delivers reproducible analysis based on linguistic and behavioral patterns rather than subjective opinion.
Can the tool analyze messages in languages other than English?
The primary operational language as indicated by the provided content is Spanish, with the interface and analysis built for Spanish-language text. The technical specifications regarding additional language support are not explicitly detailed in the provided context. For accurate analysis, users should consult the platform's official documentation or support channels for the current list of supported languages and their respective processing capabilities.
What kind of input does the system accept for analysis?
The platform accepts three primary input modalities: 1) Direct text paste, where users copy and paste the message thread into a designated field. 2) Screenshot upload, utilizing OCR to extract text from an image of the conversation. 3) Contextual description, where users can narratively describe the situation and the communication in question. The system is engineered to parse and derive insights from all these structured and unstructured data formats.
securememo.app FAQ
How does the encryption work technically?
The encryption process is executed entirely within your web browser. When you create a memo, the application generates a strong, random encryption key locally. Your text is then encrypted with this key using advanced standards (like AES-256-GCM) before it is ever sent over the internet to securememo.app's servers. The service only stores and transmits this encrypted ciphertext. The decryption key is presented to you as a password, which must be shared separately with the recipient to unlock the note.
What happens if the recipient loses the password?
Due to the zero-knowledge architecture, the password for decrypting the memo exists only with the creator and the recipient. Securememo.app's servers never receive or store this password. Therefore, if the password is lost, there is absolutely no technical way for anyone, including the service administrators, to recover the contents of the encrypted memo. The data remains cryptographically secure and permanently inaccessible.
Are there any limits on memo size or content?
While specific limits are subject to the service's operational policy, typical constraints for such a service involve a maximum character count for the memo body (e.g., several thousand characters) to ensure performance and manage server storage for the encrypted text. The content is usually plain text, and the service is designed for textual data rather than file attachments. Users should consult the application interface for the exact, current limitations.
How is the "self-destruct" mechanism enforced?
Once a memo is created, it is stored on securememo.app's servers in its encrypted state. The system is programmed to permanently delete the encrypted data from its databases immediately after the unique access link is used successfully (i.e., the correct password is entered and the note is decrypted and displayed for the first time). This deletion is automatic, irreversible, and is a fundamental part of the data processing workflow.
