Phishly vs Yardyly
Side-by-side comparison to help you choose the right tool.
Phishly
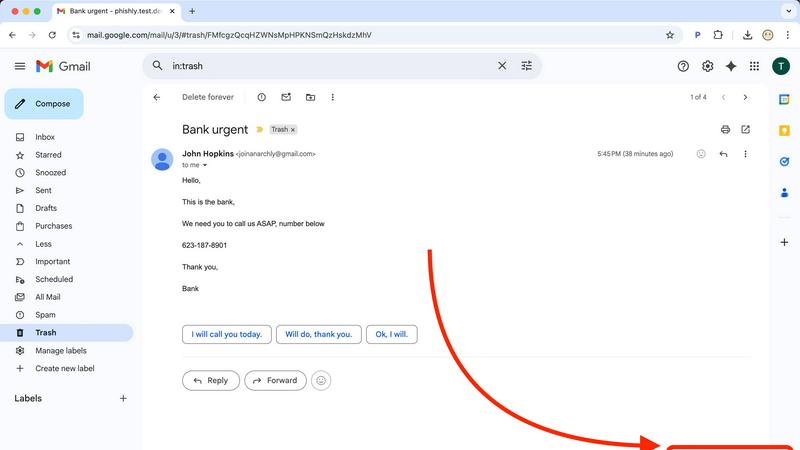
Phishly is an AI-powered Chrome extension that instantly detects phishing emails in Gmail.
Yardyly is a comprehensive software platform that centralizes and streamlines all operational, financial, and project.
Last updated: March 4, 2026
Visual Comparison
Phishly
Yardyly

Feature Comparison
Phishly
AI-Powered Multi-Indicator Detection Engine
The platform's core analytical capability is driven by an advanced AI engine that scans for a comprehensive array of phishing signatures. This includes technical indicators like domain spoofing, mismatched sender addresses, and suspicious URL structures. Furthermore, it performs semantic analysis to detect social engineering tactics such as urgent or threatening language, impersonation of authority figures, and offers that seem too good to be true. The model is continuously updated to recognize emerging phishing patterns and zero-day social engineering campaigns, providing a dynamic defense that improves over time.
Seamless Gmail Integration via Chrome Extension
Phishly offers a native Chrome extension that adds a dedicated "Scan with Phishly" button directly within the Gmail web interface. This feature allows for one-click analysis of any open email thread without requiring the user to copy, paste, or leave their inbox. The extension maintains a minimal footprint, operating only upon explicit user activation. This integration streamlines the security check into the user's existing email workflow, eliminating friction and encouraging regular use for suspicious messages.
Privacy-First, On-Demand Scanning Protocol
A foundational feature of Phishly is its strict privacy-centric operational model. Unlike security suites that scan all incoming mail automatically, Phishly employs an explicit consent framework. The AI algorithms are activated solely when a user manually initiates a scan via the extension or web tool. This ensures complete user control over data sharing, with no passive monitoring, email storage, or analysis of correspondence beyond the single submitted message. This design addresses critical privacy concerns for professionals handling sensitive communications.
Clear, Actionable Risk Assessment Reports
Upon analysis, Phishly generates a detailed diagnostic report that transcends a simple pass/fail alert. Each scan result is categorized into a clear risk tier: Safe, Medium Risk, or High Risk. The report elaborates with specific, plain-language explanations for the verdict, pinpointing exact issues found, such as "The sender's domain 'paypa1-security.com' is a homoglyph attack impersonating 'paypal.com'" or "The message uses high-pressure language demanding immediate action." This educational component helps users understand the threat and learn to identify similar attempts in the future.
Yardyly
Unified Operational Dashboard
The platform provides a single-pane-of-glass dashboard that delivers a comprehensive, real-time overview of all business activities. This includes visual tracking of daily schedules, active job statuses, team member locations and assignments, pending invoices, and key performance indicators (KPIs). The interface is designed for intuitive drag-and-drop functionality, allowing managers to quickly reassign resources, reschedule appointments, and update job priorities without navigating through multiple menus, thereby optimizing daily operational decision-making.
Automated Scheduling & Dispatch
Yardyly features an intelligent scheduling engine that automates the assignment and routing of jobs. Managers can visually plot and optimize routes for their crews using the drag-and-drop calendar, minimizing travel time and fuel costs. The system automatically sends dispatch notifications and job details to field teams' mobile devices. This feature includes conflict detection to prevent double-booking and allows for recurring service scheduling, ensuring efficient resource allocation and predictable workflow management.
Integrated CRM & Client Portal
This feature consolidates all client interactions and data into a centralized customer relationship management (CRM) module. It maintains detailed client profiles, service history, notes, and preferences. The integrated client portal facilitates professional online booking, enables clients to view estimates and invoices, and provides a secure channel for communication and feedback submission. This direct integration of client feedback into the operational workflow allows for immediate issue resolution and service quality enhancement.
Financial Management & Invoicing Suite
Yardyly includes a robust financial toolkit that automates the billing cycle. It generates and sends professional, branded invoices directly from scheduled jobs or completed work orders. The system tracks all financial transactions, including client payments, supplier contract costs, and equipment expenses. It supports multiple payment gateways for online payments and provides detailed financial reporting for precise fiscal control, cash flow analysis, and simplified tax preparation.
Use Cases
Phishly
Verification of Financial and Invoice Emails
Users frequently receive emails purporting to be from banks, payment processors like PayPal, or vendors with urgent invoice updates. These are prime targets for phishing. With Phishly, a user can instantly scan such an email to verify the legitimacy of the sender's domain, check for subtle misspellings in links, and assess whether the tone matches a genuine financial alert. This use case is critical for preventing business email compromise (BEC) and direct financial fraud.
Screening Potential Credential Theft Attempts
A common phishing vector involves fake login pages for services like Microsoft 365, Google, Dropbox, or social media. Phishly analyzes emails containing login prompts or password reset requests. It examines the embedded links for authenticity and checks if the email's headers and content align with the official communication patterns of the service being impersonated, helping users avoid surrendering their credentials to malicious actors.
Analyzing Unsolicited Job Offers or Prize Notifications
Suspicious job offers, grant opportunities, or prize win notifications are often used as lures. Individuals, especially freelancers and job seekers, can use Phishly to scrutinize these emails. The AI detects hallmarks of such scams, including poorly written content, requests for personal information upfront, and links to unverified domains, protecting users from advance-fee fraud and identity theft schemes.
Educational Tool for Security Awareness Training
For small business owners or team leads, Phishly serves as a practical, real-world training tool. When a suspicious email is received, teams can use the web tool to analyze it together. The detailed breakdown provided in the risk report educates employees on the specific tactics used by phishers, such as sender spoofing or deceptive link text, thereby building a more security-conscious organizational culture through hands-on experience.
Yardyly
Scaling a Solo Landscaping Operation
For a solo entrepreneur or a small start-up, Yardyly automates the administrative foundation of the business. The owner can manage online bookings, automatically schedule their own week, send digital estimates and invoices, and track all expenses from a single mobile device. This eliminates manual data entry and reduces time spent on paperwork, allowing the sole operator to focus entirely on service delivery and client acquisition while maintaining a professional, organized business front.
Managing a Multi-Crew Lawn Care Business
A growing business with several field crews utilizes Yardyly for centralized dispatch and real-time coordination. The manager can assign jobs, optimize daily routes for multiple teams, and track each crew's progress and location from the office dashboard. Field technicians receive job details digitally, update statuses upon completion, and can log materials used. This use case streamlines communication, reduces radio traffic, and provides management with instant visibility into field operations and productivity.
Streamlining Client Communication and Billing
Service businesses use Yardyly to professionalize client interactions and accelerate cash flow. The client portal allows customers to book services, view upcoming appointments, and access their service history. Automated invoicing triggered by job completion, coupled with integrated online payment options, significantly reduces the payment cycle. Centralized communication logs ensure all client requests and feedback are tracked and addressed, enhancing customer satisfaction and retention rates.
Overseeing Project-Based Landscape Installations
For companies handling complex, multi-phase projects like landscape installations, Yardyly provides project coordination tools. Managers can break down projects into tracked tasks, assign them to specific team members with deadlines, and monitor overall project status, budget adherence, and resource allocation. This use case ensures that large projects remain on schedule and within budget, while facilitating collaboration and accountability across the team.
Overview
About Phishly
Phishly is a specialized AI-powered cybersecurity platform engineered to provide real-time phishing detection and analysis. Its core architecture is built around a multi-layered machine learning model trained to identify sophisticated phishing indicators that often evade traditional spam filters. The platform is delivered through two primary interfaces: a lightweight Chrome browser extension that integrates directly with Gmail's web interface and a standalone web application for analyzing email content pasted from any source. This dual-access model ensures comprehensive coverage for users regardless of their email client or workflow. Phishly is specifically designed for individuals, remote workers, freelancers, and small to medium-sized businesses that require enterprise-grade security analysis without the associated complexity, cost, or IT overhead. Its fundamental value proposition lies in its on-demand, privacy-centric scanning model; the AI only processes emails that a user explicitly submits for review, ensuring no background data collection or unauthorized access to the inbox. The system delivers a clear, triage-based risk assessment (Safe, Medium Risk, High Risk) accompanied by a granular breakdown of detected threats, empowering users with actionable intelligence to make informed security decisions instantly.
About Yardyly
Yardyly is a comprehensive, cloud-based business management platform engineered specifically for the operational demands of the landscaping, lawn care, and outdoor service industries. It functions as a centralized digital hub, consolidating critical business functions that are typically fragmented across disparate systems. The platform is architected to replace inefficient manual processes involving spreadsheets, paper notes, and multiple disconnected applications. Its core value proposition lies in automating administrative tasks, enhancing operational clarity, and improving communication channels, thereby enabling business owners and managers to reallocate time from chaotic logistics to revenue-generating activities and business growth. Yardyly is designed with scalability in mind, serving solo operators establishing their business as effectively as it supports growing teams managing complex schedules and client portfolios. Its mobile-responsive design ensures full platform functionality is accessible from any device, providing real-time management capabilities from the field or the office. The software's integration of online booking, job scheduling, customer relationship management (CRM), invoicing, and team coordination tools creates a seamless workflow from client acquisition to job completion and payment.
Frequently Asked Questions
Phishly FAQ
How does Phishly protect my privacy compared to other security tools?
Phishly is architected with a strict on-demand analysis model. The system has no access to your email account or inbox. Scanning is only performed on the specific email content you actively choose to submit, either by clicking the extension button in an open Gmail or by pasting text into the web tool. We do not store, log, or analyze any email you do not explicitly send for review. This ensures maximum user control and data privacy.
What specific indicators does the AI look for in an email?
The AI engine conducts a multi-faceted analysis. Technically, it examines email headers for spoofing (e.g., mismatched 'From' addresses), analyzes domain names for homoglyphs and typosquatting, and inspects URLs for redirects and suspicious registrations. Linguistically, it uses Natural Language Processing (NLP) to flag social engineering tactics, including urgency, fear, greed, impersonation of trusted entities, and grammatical inconsistencies atypical of legitimate corporate communications.
Is technical knowledge required to install and use Phishly?
No technical expertise is required. Installation involves adding the Phishly Chrome extension from the Chrome Web Store with a single click. Usage is equally straightforward: within Gmail, simply open any email and click the "Scan with Phishly" button. For emails outside Gmail, copy the full email text and paste it into the analysis field on the Phishly website. The interface and risk reports are designed for clarity for all user levels.
What is the difference between the 'Medium Risk' and 'High Risk' classifications?
A 'Medium Risk' classification indicates the email contains one or more suspicious characteristics but may not be a definitive phishing attempt. Examples include a slightly unusual sender domain, mildly urgent language, or a link to a newly registered but not overtly malicious site. A 'High Risk' classification is assigned when multiple, strong phishing indicators are conclusively identified, such as confirmed domain spoofing, links to known malicious infrastructure, or a clear replica of a legitimate service's login page. The detailed report explains the specific findings behind the rating.
Yardyly FAQ
What makes Yardyly different from generic business management software?
Yardyly is engineered from the ground up for the specific workflows and challenges of the green industry. Unlike generic software, it includes native features for job scheduling with geographic route optimization, client portals for service history and lawn care plans, equipment and material tracking, and integrated feedback loops specific to service quality. This industry-specific design reduces customization needs and ensures the platform aligns perfectly with standard landscaping and lawn care business processes.
Is my business data secure on the Yardyly platform?
Yes, Yardyly employs enterprise-grade security protocols to protect your data. This includes SSL (Secure Sockets Layer) encryption for all data transmitted between your device and our servers, ensuring that sensitive information like client details and financial data is secured in transit. The platform is hosted on reliable, secure cloud infrastructure with regular backups. Access is controlled through secure login credentials, and you maintain full ownership of all your business data entered into the system.
Can I use Yardyly on mobile devices in the field?
Absolutely. Yardyly is built with a fully responsive, mobile-friendly design. The entire platform, including the scheduling calendar, job details, client information, and time-tracking tools, is accessible and fully functional on smartphones and tablets. This allows field crews to view their assigned routes, update job statuses in real-time, log notes or photos, and communicate with the office without needing to return to a desktop computer, ensuring operational continuity from any location.
How does the onboarding and setup process work?
Yardyly offers a customizable setup process. After signing up, you can tailor the application to your specific business needs by configuring service types, pricing models, invoice templates, and user roles. The platform is designed for intuitive use, but comprehensive support resources are available. You can import existing client lists and begin scheduling jobs immediately. The drag-and-drop interface allows for a low-learning-curve adoption, enabling you to streamline operations quickly without extensive training.