FilexHost vs Phishly
Side-by-side comparison to help you choose the right tool.
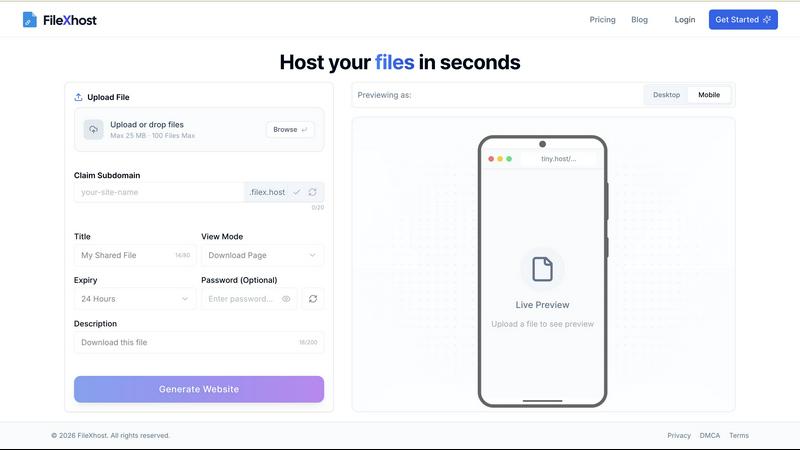
FilexHost
FilexHost lets you effortlessly upload and share files with instant, customizable URLs in just seconds.
Last updated: February 26, 2026
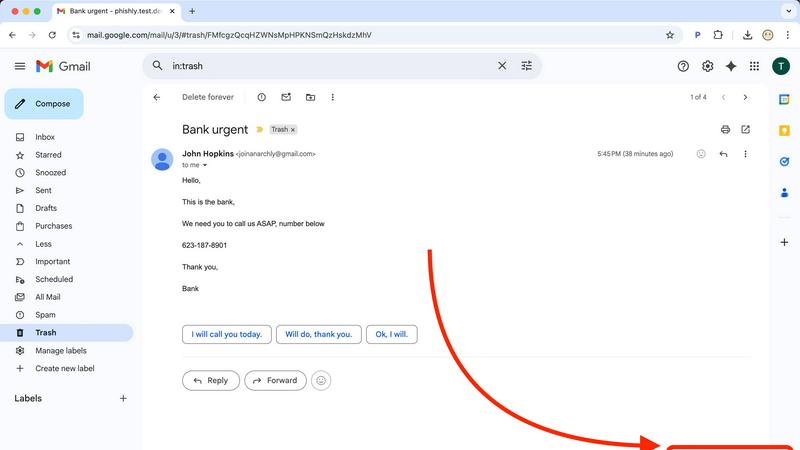
Phishly
Phishly is an AI-powered Chrome extension that instantly detects phishing emails in Gmail.
Visual Comparison
FilexHost
Phishly
Feature Comparison
FilexHost
Universal File Support
FilexHost accommodates a wide range of file types, including PDFs, Excel sheets, images, media files, and HTML projects. Its smart rendering engine ensures that each file type is displayed optimally, whether it is an interactive spreadsheet or a streaming video, thereby enhancing the viewing experience for recipients.
Instant Subdomains
Upon file upload, users receive a unique subdomain (your-file.filex.host) with zero setup required. This feature allows for quick and easy access to shared files, ensuring that recipients can view or download content without navigating complex URLs or directories.
Secure File Sharing
Every link generated by FilexHost is protected by free SSL encryption, ensuring that files are transmitted securely. Users can also opt for additional security measures such as password protection and expiration settings, giving them control over who can access their files and for how long.
Built-In Analytics
The Pro Plan offers users built-in analytics that provide insights into views and downloads of hosted files. This feature is particularly beneficial for businesses and creators who want to track engagement and optimize their content sharing strategies based on actual user interactions.
Phishly
AI-Powered Multi-Indicator Detection Engine
The platform's core analytical capability is driven by an advanced AI engine that scans for a comprehensive array of phishing signatures. This includes technical indicators like domain spoofing, mismatched sender addresses, and suspicious URL structures. Furthermore, it performs semantic analysis to detect social engineering tactics such as urgent or threatening language, impersonation of authority figures, and offers that seem too good to be true. The model is continuously updated to recognize emerging phishing patterns and zero-day social engineering campaigns, providing a dynamic defense that improves over time.
Seamless Gmail Integration via Chrome Extension
Phishly offers a native Chrome extension that adds a dedicated "Scan with Phishly" button directly within the Gmail web interface. This feature allows for one-click analysis of any open email thread without requiring the user to copy, paste, or leave their inbox. The extension maintains a minimal footprint, operating only upon explicit user activation. This integration streamlines the security check into the user's existing email workflow, eliminating friction and encouraging regular use for suspicious messages.
Privacy-First, On-Demand Scanning Protocol
A foundational feature of Phishly is its strict privacy-centric operational model. Unlike security suites that scan all incoming mail automatically, Phishly employs an explicit consent framework. The AI algorithms are activated solely when a user manually initiates a scan via the extension or web tool. This ensures complete user control over data sharing, with no passive monitoring, email storage, or analysis of correspondence beyond the single submitted message. This design addresses critical privacy concerns for professionals handling sensitive communications.
Clear, Actionable Risk Assessment Reports
Upon analysis, Phishly generates a detailed diagnostic report that transcends a simple pass/fail alert. Each scan result is categorized into a clear risk tier: Safe, Medium Risk, or High Risk. The report elaborates with specific, plain-language explanations for the verdict, pinpointing exact issues found, such as "The sender's domain 'paypa1-security.com' is a homoglyph attack impersonating 'paypal.com'" or "The message uses high-pressure language demanding immediate action." This educational component helps users understand the threat and learn to identify similar attempts in the future.
Use Cases
FilexHost
Professional Reporting
Professionals can use FilexHost to share client reports and presentations effortlessly. The platform's drag-and-drop functionality allows for quick uploads, while secure links ensure confidential information is shared safely.
Developer Hosting
Developers can host landing pages, mock APIs, or even entire websites without any server configuration. The instant subdomain feature makes it easy to share projects with clients or team members, facilitating seamless collaboration.
Digital Product Distribution
Creators can distribute digital products, such as e-books or design files, without attachment limits or complicated sharing processes. With password protection and file expiry options, they can manage access to their products efficiently.
File Backup and Sharing
Users looking to back up important files or share large files with friends or colleagues can utilize FilexHost for a hassle-free experience. The platform allows for hosting and sharing of files up to 1GB, making it suitable for medium-sized projects or multimedia content.
Phishly
Verification of Financial and Invoice Emails
Users frequently receive emails purporting to be from banks, payment processors like PayPal, or vendors with urgent invoice updates. These are prime targets for phishing. With Phishly, a user can instantly scan such an email to verify the legitimacy of the sender's domain, check for subtle misspellings in links, and assess whether the tone matches a genuine financial alert. This use case is critical for preventing business email compromise (BEC) and direct financial fraud.
Screening Potential Credential Theft Attempts
A common phishing vector involves fake login pages for services like Microsoft 365, Google, Dropbox, or social media. Phishly analyzes emails containing login prompts or password reset requests. It examines the embedded links for authenticity and checks if the email's headers and content align with the official communication patterns of the service being impersonated, helping users avoid surrendering their credentials to malicious actors.
Analyzing Unsolicited Job Offers or Prize Notifications
Suspicious job offers, grant opportunities, or prize win notifications are often used as lures. Individuals, especially freelancers and job seekers, can use Phishly to scrutinize these emails. The AI detects hallmarks of such scams, including poorly written content, requests for personal information upfront, and links to unverified domains, protecting users from advance-fee fraud and identity theft schemes.
Educational Tool for Security Awareness Training
For small business owners or team leads, Phishly serves as a practical, real-world training tool. When a suspicious email is received, teams can use the web tool to analyze it together. The detailed breakdown provided in the risk report educates employees on the specific tactics used by phishers, such as sender spoofing or deceptive link text, thereby building a more security-conscious organizational culture through hands-on experience.
Overview
About FilexHost
FilexHost is an innovative file hosting and sharing platform that simplifies the process of distributing files of any type, ranging from documents to multimedia files. With its intuitive "Drop & Share" workflow, users can easily drag and drop files, instantly generating a secure URL for sharing without the need for complex setups, server management, or user logins. This makes FilexHost an ideal solution for professionals, developers, and creators who require a reliable and efficient way to share content without facing the limitations of traditional file sharing methods. The platform supports a variety of file formats, ensuring optimal rendering for each type, and prioritizes user experience by presenting files beautifully and functionally. Additionally, FilexHost offers robust security features, including free SSL encryption, making it a trustworthy option for anyone looking to share files securely.
About Phishly
Phishly is a specialized AI-powered cybersecurity platform engineered to provide real-time phishing detection and analysis. Its core architecture is built around a multi-layered machine learning model trained to identify sophisticated phishing indicators that often evade traditional spam filters. The platform is delivered through two primary interfaces: a lightweight Chrome browser extension that integrates directly with Gmail's web interface and a standalone web application for analyzing email content pasted from any source. This dual-access model ensures comprehensive coverage for users regardless of their email client or workflow. Phishly is specifically designed for individuals, remote workers, freelancers, and small to medium-sized businesses that require enterprise-grade security analysis without the associated complexity, cost, or IT overhead. Its fundamental value proposition lies in its on-demand, privacy-centric scanning model; the AI only processes emails that a user explicitly submits for review, ensuring no background data collection or unauthorized access to the inbox. The system delivers a clear, triage-based risk assessment (Safe, Medium Risk, High Risk) accompanied by a granular breakdown of detected threats, empowering users with actionable intelligence to make informed security decisions instantly.
Frequently Asked Questions
FilexHost FAQ
What is FilexHost?
FilexHost is a file hosting and sharing service that allows users to upload, share, and manage files of various types through an intuitive interface, all without the need for complex setups or software installations.
Is it really free?
Yes, FilexHost offers a free plan that allows users to host up to 1,000 files with a maximum size of 25MB each for up to 7 days. This plan includes ads but provides a straightforward solution for quick file sharing.
What file types are supported?
FilexHost supports a wide array of file types, including PDFs, Excel sheets, images (JPG, PNG, WEBP), audio (MP3), video (MP4), and HTML projects. This versatility makes it suitable for various use cases, from documents to multimedia files.
How do I update my site?
To update your site or hosted file, simply upload the new version using the drag-and-drop feature. FilexHost will generate a new link for the updated file, ensuring that your recipients always have access to the latest version without any additional steps.
Phishly FAQ
How does Phishly protect my privacy compared to other security tools?
Phishly is architected with a strict on-demand analysis model. The system has no access to your email account or inbox. Scanning is only performed on the specific email content you actively choose to submit, either by clicking the extension button in an open Gmail or by pasting text into the web tool. We do not store, log, or analyze any email you do not explicitly send for review. This ensures maximum user control and data privacy.
What specific indicators does the AI look for in an email?
The AI engine conducts a multi-faceted analysis. Technically, it examines email headers for spoofing (e.g., mismatched 'From' addresses), analyzes domain names for homoglyphs and typosquatting, and inspects URLs for redirects and suspicious registrations. Linguistically, it uses Natural Language Processing (NLP) to flag social engineering tactics, including urgency, fear, greed, impersonation of trusted entities, and grammatical inconsistencies atypical of legitimate corporate communications.
Is technical knowledge required to install and use Phishly?
No technical expertise is required. Installation involves adding the Phishly Chrome extension from the Chrome Web Store with a single click. Usage is equally straightforward: within Gmail, simply open any email and click the "Scan with Phishly" button. For emails outside Gmail, copy the full email text and paste it into the analysis field on the Phishly website. The interface and risk reports are designed for clarity for all user levels.
What is the difference between the 'Medium Risk' and 'High Risk' classifications?
A 'Medium Risk' classification indicates the email contains one or more suspicious characteristics but may not be a definitive phishing attempt. Examples include a slightly unusual sender domain, mildly urgent language, or a link to a newly registered but not overtly malicious site. A 'High Risk' classification is assigned when multiple, strong phishing indicators are conclusively identified, such as confirmed domain spoofing, links to known malicious infrastructure, or a clear replica of a legitimate service's login page. The detailed report explains the specific findings behind the rating.
