Phishly vs Zovo
Side-by-side comparison to help you choose the right tool.
Phishly
Phishly is an AI-powered Chrome extension that instantly detects phishing emails in Gmail.
Zovo offers 20 privacy-first Chrome extensions for developers and writers, all accessible with a single subscription.
Last updated: February 26, 2026
Visual Comparison
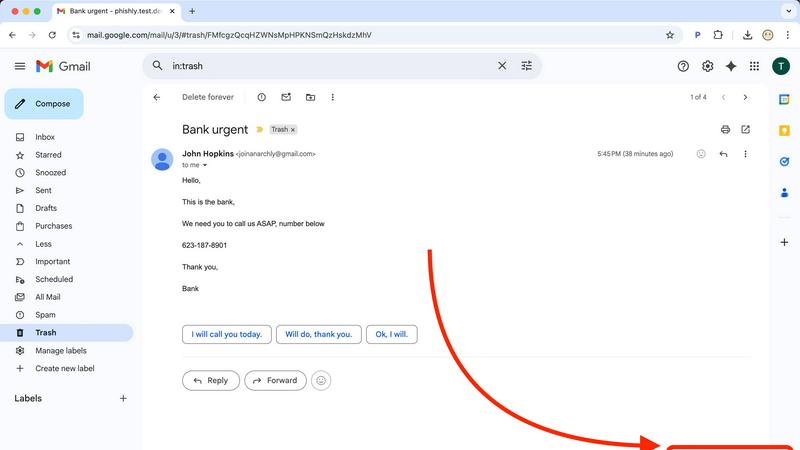
Phishly
Zovo
Feature Comparison
Phishly
AI-Powered Multi-Indicator Detection Engine
The platform's core analytical capability is driven by an advanced AI engine that scans for a comprehensive array of phishing signatures. This includes technical indicators like domain spoofing, mismatched sender addresses, and suspicious URL structures. Furthermore, it performs semantic analysis to detect social engineering tactics such as urgent or threatening language, impersonation of authority figures, and offers that seem too good to be true. The model is continuously updated to recognize emerging phishing patterns and zero-day social engineering campaigns, providing a dynamic defense that improves over time.
Seamless Gmail Integration via Chrome Extension
Phishly offers a native Chrome extension that adds a dedicated "Scan with Phishly" button directly within the Gmail web interface. This feature allows for one-click analysis of any open email thread without requiring the user to copy, paste, or leave their inbox. The extension maintains a minimal footprint, operating only upon explicit user activation. This integration streamlines the security check into the user's existing email workflow, eliminating friction and encouraging regular use for suspicious messages.
Privacy-First, On-Demand Scanning Protocol
A foundational feature of Phishly is its strict privacy-centric operational model. Unlike security suites that scan all incoming mail automatically, Phishly employs an explicit consent framework. The AI algorithms are activated solely when a user manually initiates a scan via the extension or web tool. This ensures complete user control over data sharing, with no passive monitoring, email storage, or analysis of correspondence beyond the single submitted message. This design addresses critical privacy concerns for professionals handling sensitive communications.
Clear, Actionable Risk Assessment Reports
Upon analysis, Phishly generates a detailed diagnostic report that transcends a simple pass/fail alert. Each scan result is categorized into a clear risk tier: Safe, Medium Risk, or High Risk. The report elaborates with specific, plain-language explanations for the verdict, pinpointing exact issues found, such as "The sender's domain 'paypa1-security.com' is a homoglyph attack impersonating 'paypal.com'" or "The message uses high-pressure language demanding immediate action." This educational component helps users understand the threat and learn to identify similar attempts in the future.
Zovo
BeLikeNative
BeLikeNative is the flagship extension that enables users to rewrite text in a single keystroke, enhancing language proficiency. It supports 80 languages and is designed to help non-native speakers communicate more effectively and naturally, making it ideal for students, professionals, and anyone looking to improve their writing skills.
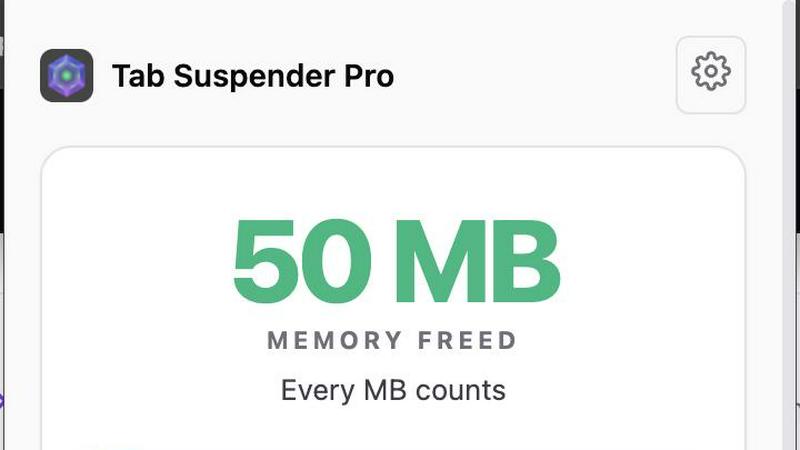
Tab Suspender Pro
Tab Suspender Pro automatically suspends inactive tabs to free up system memory, enhancing browser performance. It employs smart detection to identify unused tabs and suspends them without losing your session. This feature is particularly beneficial for users who work with multiple tabs open and need to manage resources efficiently.
JSON Formatter Pro
JSON Formatter Pro is a powerful tool for formatting, validating, and exploring JSON data directly in your browser. It offers features like beautification, minification, and a tree explorer for easy navigation of complex JSON structures. This extension is perfect for developers and data analysts who work with APIs and need to manipulate JSON data frequently.
Clipboard History Pro
Clipboard History Pro allows users to save and manage an extensive history of copied text, supporting up to 10,000 clips. It features instant search capabilities and smart paste functionality, which makes retrieving and using previously copied content quick and easy. This tool is invaluable for writers, researchers, and anyone who regularly copies and pastes information.
Use Cases
Phishly
Verification of Financial and Invoice Emails
Users frequently receive emails purporting to be from banks, payment processors like PayPal, or vendors with urgent invoice updates. These are prime targets for phishing. With Phishly, a user can instantly scan such an email to verify the legitimacy of the sender's domain, check for subtle misspellings in links, and assess whether the tone matches a genuine financial alert. This use case is critical for preventing business email compromise (BEC) and direct financial fraud.
Screening Potential Credential Theft Attempts
A common phishing vector involves fake login pages for services like Microsoft 365, Google, Dropbox, or social media. Phishly analyzes emails containing login prompts or password reset requests. It examines the embedded links for authenticity and checks if the email's headers and content align with the official communication patterns of the service being impersonated, helping users avoid surrendering their credentials to malicious actors.
Analyzing Unsolicited Job Offers or Prize Notifications
Suspicious job offers, grant opportunities, or prize win notifications are often used as lures. Individuals, especially freelancers and job seekers, can use Phishly to scrutinize these emails. The AI detects hallmarks of such scams, including poorly written content, requests for personal information upfront, and links to unverified domains, protecting users from advance-fee fraud and identity theft schemes.
Educational Tool for Security Awareness Training
For small business owners or team leads, Phishly serves as a practical, real-world training tool. When a suspicious email is received, teams can use the web tool to analyze it together. The detailed breakdown provided in the risk report educates employees on the specific tactics used by phishers, such as sender spoofing or deceptive link text, thereby building a more security-conscious organizational culture through hands-on experience.
Zovo
Enhancing Language Skills
BeLikeNative is ideal for language learners who wish to improve their writing skills. By offering instant rewrites in multiple languages, users can learn contextually appropriate phrasing and grammar while communicating in foreign languages, enhancing their overall fluency.
Managing Browser Performance
Tab Suspender Pro is a must-have for users who often have numerous tabs open for research or multitasking. By automatically managing inactive tabs, it prevents system slowdowns, allowing users to maintain focus and productivity without worrying about memory overload.
Simplifying JSON Manipulation
Developers and data analysts can leverage JSON Formatter Pro to streamline their workflow when dealing with JSON data. Whether it is for API testing or data validation, this extension provides the tools necessary to handle JSON efficiently, saving time and reducing errors.
Improving Productivity with Clipboard Management
Clipboard History Pro is perfect for professionals who handle large volumes of text, such as writers or marketers. By keeping track of all copied content, users can easily retrieve and reuse information, making their work process faster and more efficient, reducing stress over lost data.
Overview
About Phishly
Phishly is a specialized AI-powered cybersecurity platform engineered to provide real-time phishing detection and analysis. Its core architecture is built around a multi-layered machine learning model trained to identify sophisticated phishing indicators that often evade traditional spam filters. The platform is delivered through two primary interfaces: a lightweight Chrome browser extension that integrates directly with Gmail's web interface and a standalone web application for analyzing email content pasted from any source. This dual-access model ensures comprehensive coverage for users regardless of their email client or workflow. Phishly is specifically designed for individuals, remote workers, freelancers, and small to medium-sized businesses that require enterprise-grade security analysis without the associated complexity, cost, or IT overhead. Its fundamental value proposition lies in its on-demand, privacy-centric scanning model; the AI only processes emails that a user explicitly submits for review, ensuring no background data collection or unauthorized access to the inbox. The system delivers a clear, triage-based risk assessment (Safe, Medium Risk, High Risk) accompanied by a granular breakdown of detected threats, empowering users with actionable intelligence to make informed security decisions instantly.
About Zovo
Zovo is a collection of 20 innovative Chrome extensions developed by Michael Lip, a solo developer with over a decade of experience in software development and a proven track record of $400K+ earned on Upwork, boasting a 100% success rate. Designed with user privacy as a cornerstone, Zovo's suite of tools ensures that your data remains local and never leaves your device, eliminating concerns about data harvesting or corporate influence. The flagship extension, BeLikeNative, helps over 3,300 users write like native speakers by providing one-keystroke rewrites in 80 languages. Zovo includes various other useful tools such as Tab Suspender Pro for memory management, JSON Formatter Pro for JSON data manipulation, and Clipboard History Pro to keep track of copied text. With a community-driven approach, users can request features that they need, shaping the future of the product. New extensions are released monthly, and many tools are also available for free at zovo.one.
Frequently Asked Questions
Phishly FAQ
How does Phishly protect my privacy compared to other security tools?
Phishly is architected with a strict on-demand analysis model. The system has no access to your email account or inbox. Scanning is only performed on the specific email content you actively choose to submit, either by clicking the extension button in an open Gmail or by pasting text into the web tool. We do not store, log, or analyze any email you do not explicitly send for review. This ensures maximum user control and data privacy.
What specific indicators does the AI look for in an email?
The AI engine conducts a multi-faceted analysis. Technically, it examines email headers for spoofing (e.g., mismatched 'From' addresses), analyzes domain names for homoglyphs and typosquatting, and inspects URLs for redirects and suspicious registrations. Linguistically, it uses Natural Language Processing (NLP) to flag social engineering tactics, including urgency, fear, greed, impersonation of trusted entities, and grammatical inconsistencies atypical of legitimate corporate communications.
Is technical knowledge required to install and use Phishly?
No technical expertise is required. Installation involves adding the Phishly Chrome extension from the Chrome Web Store with a single click. Usage is equally straightforward: within Gmail, simply open any email and click the "Scan with Phishly" button. For emails outside Gmail, copy the full email text and paste it into the analysis field on the Phishly website. The interface and risk reports are designed for clarity for all user levels.
What is the difference between the 'Medium Risk' and 'High Risk' classifications?
A 'Medium Risk' classification indicates the email contains one or more suspicious characteristics but may not be a definitive phishing attempt. Examples include a slightly unusual sender domain, mildly urgent language, or a link to a newly registered but not overtly malicious site. A 'High Risk' classification is assigned when multiple, strong phishing indicators are conclusively identified, such as confirmed domain spoofing, links to known malicious infrastructure, or a clear replica of a legitimate service's login page. The detailed report explains the specific findings behind the rating.
Zovo FAQ
What privacy measures does Zovo implement?
Zovo is committed to user privacy, ensuring that all data stays on your device and is not harvested or shared with third parties. This privacy-first approach means no corporate investors influence how your data is used.
How can users request new features?
Users can submit feature requests directly to the developer, Michael Lip. Each request is reviewed, and the most requested features are prioritized for development, allowing the community to have a direct impact on the product's roadmap.
Are there any free tools available?
Yes, Zovo offers many tools for free, which can be accessed at zovo.one. This allows users to try out the product's functionality before committing to any paid options.
How often are new extensions released?
Zovo releases new extensions on a monthly basis, with members often receiving early access 1-2 weeks before the public release. This ensures that users are always getting the latest tools and features as soon as they are available.
