finban vs Threat Watch
Side-by-side comparison to help you choose the right tool.
finban simplifies liquidity planning, enabling confident decisions on hiring, taxes, and investments without Excel.
Last updated: February 26, 2026
Threat Watch
Threat Watch instantly analyzes your cybersecurity posture across credentials, devices, and dark web exposures.
Last updated: March 1, 2026
Visual Comparison
finban
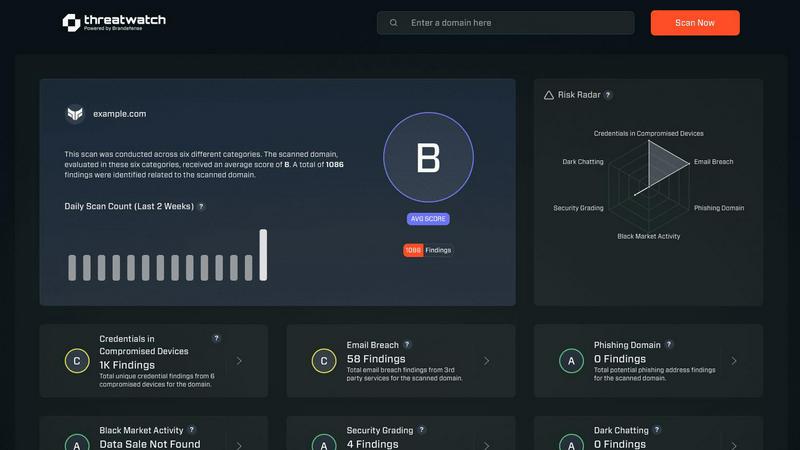
Threat Watch
Feature Comparison
finban
Liquidity OS
Liquidity OS is the core of finban, providing detailed visibility into daily cash inflows and outflows. It allows businesses to track their liquidity in real time, ensuring that financial decisions are made with a clear understanding of available resources. This feature helps mitigate risks associated with cash flow uncertainty.
Scenarios
The Scenarios feature enables users to simulate various financial options by asking "What happens if...?" questions. This tool helps businesses visualize potential outcomes and their impact on liquidity, transforming gut feelings into data-driven decisions. Users can quickly assess the implications of different strategies and choose the most effective one.
Budget Management
With finban's Budget Management feature, users can connect planning with actual figures, identifying deviations immediately. This integration ensures that financial planning remains grounded in reality, allowing businesses to adjust their budgets proactively based on real-time performance metrics.
Smart Forecasts
Smart Forecasts automatically update financial predictions based on the latest data, eliminating the need for time-consuming manual updates. This feature keeps forecasts relevant and accurate, empowering businesses to make timely decisions that align with their current financial situation.
Threat Watch
Continuous Attack Surface Monitoring
Threat Watch performs non-stop, automated discovery and inventory of all external-facing digital assets linked to an organization, including domains, subdomains, IP addresses, and cloud instances. It employs advanced reconnaissance techniques to map the entire attack surface, ensuring no asset goes unmonitored. This continuous scanning provides a real-time, dynamic view of potential entry points for adversaries, forming the foundational layer for all subsequent security analysis and threat detection processes.
Unified Threat Intelligence Correlation
The platform's core engine aggregates raw data from a multitude of sources, including proprietary scanners, breach databases, phishing feeds, and dark web monitoring. It then applies correlation algorithms and contextual analysis to transform this data into prioritized intelligence. By linking a compromised credential found on the dark web to a vulnerable server in the IT inventory, Threat Watch provides a complete narrative of risk, moving beyond isolated alerts to deliver a comprehensive understanding of interconnected threats.
Automated Exposure Assessment & Prioritization
Threat Watch automatically assesses identified exposures against severity and impact criteria, assigning a risk score to each finding. It utilizes a rules-based prioritization engine that factors in asset criticality, exploit availability, and threat actor activity. This automation eliminates alert fatigue by surfacing only the most critical issues that require immediate intervention, allowing security teams to focus their resources effectively on remediating the vulnerabilities that pose the greatest business risk.
Real-Time Alerting and Integrations
The platform provides configurable, real-time alerting via email, SMS, and integration with popular Security Information and Event Management (SIEM) systems and ticketing platforms like ServiceNow and Jira. This ensures that critical findings are routed directly into existing security workflows and incident response procedures without delay. The API-first design allows for seamless data exchange with other security tools, enabling Threat Watch to function as a central intelligence hub within a broader security architecture.
Use Cases
finban
Financial Decision-Making
finban is ideal for companies looking to streamline their financial decision-making processes. By providing a clear picture of cash flow and liquidity, users can confidently make decisions regarding hiring, investments, and project funding without the stress of uncertain financial data.
Scenario Planning
Organizations can leverage the Scenario Planning feature to explore potential futures based on varying assumptions. This is particularly useful for businesses facing market volatility or planning significant changes, allowing them to prepare alternative strategies and their financial implications.
Budget Tracking
Companies can use finban to enhance their budget tracking capabilities. By syncing actual expenditures with planned budgets, businesses can quickly identify and address discrepancies, ensuring better financial discipline and resource allocation.
Consolidated Financial Overview
For businesses managing multiple accounts or subsidiaries, finban provides a consolidated view of all financial data in one place. This feature simplifies financial oversight, enabling stakeholders to monitor cash positions and forecasts across the entire organization effortlessly.
Threat Watch
Proactive External Risk Management for CISOs
CISOs and risk management leaders utilize Threat Watch to gain a continuous, board-ready overview of the organization's external cyber risk posture. The platform provides quantified metrics and trending data on exposure categories, enabling informed decision-making on security investments and resource allocation. It supports compliance reporting and demonstrates due diligence by providing evidence of proactive monitoring and management of digital risks beyond the corporate firewall.
Accelerated Incident Response and Threat Hunting
Security Operations Center (SOC) analysts and incident responders use Threat Watch to rapidly investigate security alerts and breaches. By providing immediate context—such as whether a compromised employee credential is actively for sale or if a breached server was previously identified as vulnerable—the platform significantly shortens investigation cycles. It serves as a critical tool for proactive threat hunting, allowing teams to search for indicators of compromise (IOCs) related to their specific organization across monitored datasets.
Third-Party and Supply Chain Risk Assessment
Organizations employ Threat Watch to evaluate the external security posture of partners, vendors, and acquisition targets. By monitoring the digital assets associated with third-party entities, security teams can identify if a supplier's exposed credentials or vulnerable systems could serve as a pivot point into their own network. This use case extends the platform's value beyond internal security to managing supply chain and ecosystem risk.
Brand Protection and Phishing Mitigation
Marketing and fraud prevention teams leverage the platform's capabilities to detect phishing campaigns and brand impersonation. Threat Watch continuously scans for fraudulent domains, phishing kits, and malicious infrastructure that mimic the organization's legitimate web properties. Early detection allows for swift takedown requests and proactive customer communication, thereby protecting the brand's reputation and reducing the success rate of social engineering attacks.
Overview
About finban
finban is a cutting-edge liquidity management tool designed to empower businesses by providing clarity and control over their financial planning. This software acts as a virtual CFO, enabling users to visualize cash flow, forecast future financial scenarios, and make informed decisions regarding hiring, taxes, projects, and investments. Tailored for entrepreneurs, financial managers, and organizations of all sizes, finban eliminates the chaos associated with traditional Excel-based financial planning. By offering real-time insights into liquidity and integrating seamlessly with various financial tools, finban helps businesses maintain a clear overview of their financial health, ensuring they can act confidently and strategically. With features that allow for scenario simulations, budget tracking, and consolidated views across multiple accounts, finban provides a comprehensive solution for modern financial management.
About Threat Watch
Threat Watch is a sophisticated, unified cybersecurity intelligence and exposure management platform engineered for enterprise IT security teams, Chief Information Security Officers (CISOs), and risk management professionals. It serves as a centralized diagnostic console for an organization's external cyber health, providing continuous, automated surveillance and analysis of its entire digital asset portfolio. The platform's architecture is designed to aggregate, normalize, and correlate disparate security signals from across the clear, deep, and dark web into a single, coherent, and actionable overview. By perpetually mapping and scanning the external attack surface, Threat Watch identifies, validates, and prioritizes critical security exposures across five core categories: compromised credentials, vulnerable internet-facing devices, breached corporate accounts, active phishing infrastructure, and dark web data leaks. This intelligence-driven approach enables organizations to transition from a reactive, incident-response model to a proactive, preventative security posture. The solution delivers real-time insights and automated risk assessments, which dramatically reduces both the Mean Time to Identify (MTTI) and Mean Time to Remediate (MTTR) critical vulnerabilities, thereby systematically hardening an organization's external defenses against evolving cyber threats.
Frequently Asked Questions
finban FAQ
What types of businesses can benefit from finban?
finban is designed for businesses of all sizes and industries that require better liquidity management and financial planning. Its features are particularly beneficial for entrepreneurs, CFOs, and financial managers looking to streamline their financial processes.
How does finban integrate with other tools?
finban offers multiple integrations with popular financial tools and software, such as banking platforms, accounting software, and project management applications. This ensures that users can consolidate their data in one place, reducing manual data entry and errors.
Is there a trial period available for finban?
Yes, finban offers a free 14-day trial period that allows users to explore its features and functionalities without any commitment. This trial helps potential customers understand how finban can meet their financial management needs before making a purchase.
How secure is the data within finban?
finban prioritizes data security and employs industry-standard security measures to protect user information. This includes encryption, secure access protocols, and regular data backups to ensure that financial data remains safe and confidential.
Threat Watch FAQ
What types of assets does Threat Watch discover and monitor?
Threat Watch automatically discovers and continuously monitors a wide range of external digital assets. This includes all owned domains and subdomains, public IP addresses, SSL certificates, cloud storage instances (e.g., AWS S3 buckets, Azure Blobs), and network infrastructure devices exposed to the internet. The discovery process is agentless and based on passive and active reconnaissance techniques, ensuring comprehensive coverage without requiring internal network access.
How does Threat Watch source its data on compromised credentials and dark web exposures?
The platform aggregates data from a vast array of sources, including continuous crawling of dark web marketplaces, forums, and paste sites; integration with commercial and proprietary breach databases; and monitoring of underground communication channels. This data is then de-duplicated, validated, and correlated with the organization's monitored assets (e.g., corporate email domains) to ensure alerts are relevant and actionable, reducing false positives.
Can Threat Watch integrate with our existing security tools?
Yes, Threat Watch is built with an API-first architecture, enabling robust integration capabilities. It offers out-of-the-box integrations with major SIEM platforms (e.g., Splunk, IBM QRadar, LogRhythm), ticketing systems (e.g., ServiceNow, Jira), and orchestration tools. This allows automated ingestion of Threat Watch intelligence into existing workflows, ensuring alerts are acted upon within established security processes and that data is available for correlation with internal telemetry.
What is the deployment process and does it require internal agents?
Threat Watch is delivered as a cloud-native Software-as-a-Service (SaaS) platform, requiring no software installation or internal deployment of agents. The setup process is typically initiated by defining the organization's digital assets (e.g., root domains, IP ranges) for monitoring. The platform then begins its automated discovery and scanning processes externally, with no impact on internal network performance or bandwidth.
Alternatives
finban Alternatives
Finban is a sophisticated liquidity planning tool designed to empower businesses in making informed financial decisions related to hiring, taxes, projects, and investments. As a leading solution in the business intelligence category, it simplifies the complexities of financial forecasting and management, eliminating the chaos often associated with spreadsheet-based approaches. Users commonly seek alternatives to finban for various reasons, including pricing structures, specific feature sets, or compatibility with existing platforms. When evaluating alternatives, it is essential to consider factors such as ease of use, integration capabilities, customer support, and the ability to scale with your business needs. A well-rounded alternative should meet your unique liquidity management requirements while providing a seamless user experience.
Threat Watch Alternatives
Threat Watch is a specialized Business Intelligence platform focused on external attack surface management and cybersecurity exposure. It provides automated, continuous diagnostics of an organization's digital footprint, prioritizing risks from credential leaks to vulnerable internet-facing assets. Organizations may seek alternatives for various operational reasons. Common drivers include budget constraints, the need for specific feature integrations, or a requirement for a platform that aligns with a different internal workflow or existing security stack. The search often centers on finding a tool that matches their unique scale and risk profile. When evaluating alternatives, key criteria should include the scope of attack surface discovery, the depth and sources of dark web and credential monitoring, the automation of risk prioritization, and the platform's ability to deliver actionable intelligence that reduces mean time to remediation. The ideal solution offers comprehensive visibility tailored to the organization's asset landscape.