Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right tool.
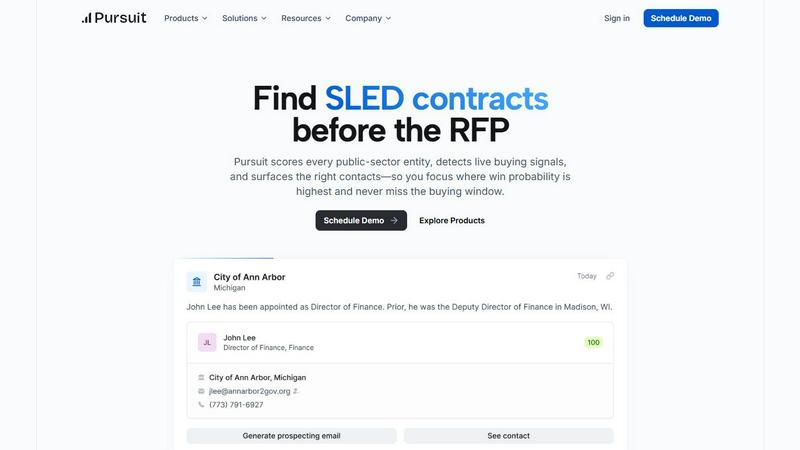
Pursuit
Pursuit leverages AI to uncover public sector sales opportunities and contacts up to 18 months before RFPs are issued.
Last updated: February 28, 2026
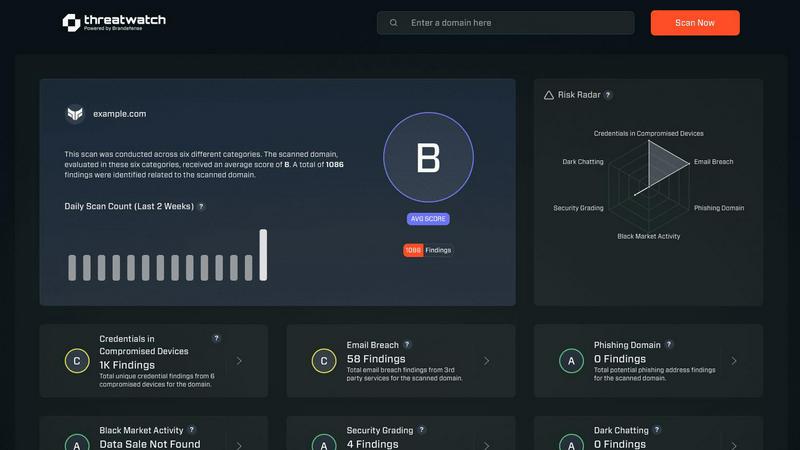
Threat Watch
Threat Watch instantly analyzes your cybersecurity posture across credentials, devices, and dark web exposures.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Pre-RFP Intelligence
Pursuit surfaces critical buying signals 6 to 18 months before RFPs are released, allowing sales teams to position themselves advantageously. By understanding the budget cycles and procurement paths of SLED entities, teams can engage early and effectively.
Advanced Data Monitoring
The platform leverages advanced AI technology to scan millions of documents daily, identifying vital intel hidden in council meetings, budget documents, and RFP postings. This capability ensures that sales teams have access to the most relevant and timely information.
Integrated Collaboration Tools
Pursuit provides integrated tools that facilitate seamless communication across go-to-market teams. When everyone operates on the same intelligence, signals flow effortlessly from awareness to closing deals and renewals, enhancing overall effectiveness.
Comprehensive Role-Specific Functionality
Designed for various personas, Pursuit offers tailored functionalities for Revenue Operations, Sales Leaders, Marketing, Account Executives, Business Development Representatives, and Customer Success teams. Each role benefits from specific features that enhance performance and productivity.
Threat Watch
Continuous Attack Surface Monitoring
Threat Watch performs non-stop, automated discovery and inventory of all external-facing digital assets linked to an organization, including domains, subdomains, IP addresses, and cloud instances. It employs advanced reconnaissance techniques to map the entire attack surface, ensuring no asset goes unmonitored. This continuous scanning provides a real-time, dynamic view of potential entry points for adversaries, forming the foundational layer for all subsequent security analysis and threat detection processes.
Unified Threat Intelligence Correlation
The platform's core engine aggregates raw data from a multitude of sources, including proprietary scanners, breach databases, phishing feeds, and dark web monitoring. It then applies correlation algorithms and contextual analysis to transform this data into prioritized intelligence. By linking a compromised credential found on the dark web to a vulnerable server in the IT inventory, Threat Watch provides a complete narrative of risk, moving beyond isolated alerts to deliver a comprehensive understanding of interconnected threats.
Automated Exposure Assessment & Prioritization
Threat Watch automatically assesses identified exposures against severity and impact criteria, assigning a risk score to each finding. It utilizes a rules-based prioritization engine that factors in asset criticality, exploit availability, and threat actor activity. This automation eliminates alert fatigue by surfacing only the most critical issues that require immediate intervention, allowing security teams to focus their resources effectively on remediating the vulnerabilities that pose the greatest business risk.
Real-Time Alerting and Integrations
The platform provides configurable, real-time alerting via email, SMS, and integration with popular Security Information and Event Management (SIEM) systems and ticketing platforms like ServiceNow and Jira. This ensures that critical findings are routed directly into existing security workflows and incident response procedures without delay. The API-first design allows for seamless data exchange with other security tools, enabling Threat Watch to function as a central intelligence hub within a broader security architecture.
Use Cases
Pursuit
Revenue Operations Optimization
Revenue Operations teams can utilize Pursuit’s 94% data accuracy and continuous enrichment capabilities to streamline data management. The native integrations with platforms like Salesforce and HubSpot ensure that data flows automatically, minimizing manual efforts.
Strategic Sales Leadership
Sales leaders can leverage Pursuit to gain visibility into which sales representatives are engaging with specific buying signals and identify any coverage gaps. This allows for more accurate forecasting and strategic decision-making based on real SLED buying indicators.
Account-Based Marketing Campaigns
Marketing teams can build targeted account-based marketing (ABM) campaigns centered around real-time buying signals, such as budget approvals and contract expirations. This strategic approach helps in maximizing conversion rates and enhancing campaign effectiveness.
Enhanced Business Development Efforts
Business Development Representatives can receive daily prioritized call lists based on actual buying signals, such as leadership changes and contract expirations. This data-driven approach eliminates guesswork and significantly increases the chances of engaging qualified leads.
Threat Watch
Proactive External Risk Management for CISOs
CISOs and risk management leaders utilize Threat Watch to gain a continuous, board-ready overview of the organization's external cyber risk posture. The platform provides quantified metrics and trending data on exposure categories, enabling informed decision-making on security investments and resource allocation. It supports compliance reporting and demonstrates due diligence by providing evidence of proactive monitoring and management of digital risks beyond the corporate firewall.
Accelerated Incident Response and Threat Hunting
Security Operations Center (SOC) analysts and incident responders use Threat Watch to rapidly investigate security alerts and breaches. By providing immediate context—such as whether a compromised employee credential is actively for sale or if a breached server was previously identified as vulnerable—the platform significantly shortens investigation cycles. It serves as a critical tool for proactive threat hunting, allowing teams to search for indicators of compromise (IOCs) related to their specific organization across monitored datasets.
Third-Party and Supply Chain Risk Assessment
Organizations employ Threat Watch to evaluate the external security posture of partners, vendors, and acquisition targets. By monitoring the digital assets associated with third-party entities, security teams can identify if a supplier's exposed credentials or vulnerable systems could serve as a pivot point into their own network. This use case extends the platform's value beyond internal security to managing supply chain and ecosystem risk.
Brand Protection and Phishing Mitigation
Marketing and fraud prevention teams leverage the platform's capabilities to detect phishing campaigns and brand impersonation. Threat Watch continuously scans for fraudulent domains, phishing kits, and malicious infrastructure that mimic the organization's legitimate web properties. Early detection allows for swift takedown requests and proactive customer communication, thereby protecting the brand's reputation and reducing the success rate of social engineering attacks.
Overview
About Pursuit
Pursuit is a cutting-edge AI-driven sales intelligence platform designed specifically for businesses targeting state, local, and educational (SLED) government entities. It tackles the unique challenges faced by public-sector sales teams, such as navigating a fragmented market consisting of over 110,000 entities, understanding complex procurement rules, and aligning outreach efforts with active buying cycles. By offering access to accurate stakeholder data and actionable insights, Pursuit empowers sales teams to focus their efforts on the highest-probability opportunities. The platform continuously monitors and analyzes public-sector data, transforming unstructured information into structured, sales-ready intelligence. Users range from individual sales representatives to executive teams in GovTech companies and established government contractors, all benefiting from Pursuit's ability to surface buying signals and budget discussions well ahead of formal RFPs. This proactive approach significantly enhances win rates and pipeline generation, allowing teams to engage with potential clients as incumbents rather than outsiders.
About Threat Watch
Threat Watch is a sophisticated, unified cybersecurity intelligence and exposure management platform engineered for enterprise IT security teams, Chief Information Security Officers (CISOs), and risk management professionals. It serves as a centralized diagnostic console for an organization's external cyber health, providing continuous, automated surveillance and analysis of its entire digital asset portfolio. The platform's architecture is designed to aggregate, normalize, and correlate disparate security signals from across the clear, deep, and dark web into a single, coherent, and actionable overview. By perpetually mapping and scanning the external attack surface, Threat Watch identifies, validates, and prioritizes critical security exposures across five core categories: compromised credentials, vulnerable internet-facing devices, breached corporate accounts, active phishing infrastructure, and dark web data leaks. This intelligence-driven approach enables organizations to transition from a reactive, incident-response model to a proactive, preventative security posture. The solution delivers real-time insights and automated risk assessments, which dramatically reduces both the Mean Time to Identify (MTTI) and Mean Time to Remediate (MTTR) critical vulnerabilities, thereby systematically hardening an organization's external defenses against evolving cyber threats.
Frequently Asked Questions
Pursuit FAQ
How does Pursuit help with identifying buying signals?
Pursuit utilizes advanced AI algorithms to continuously monitor public documents and discussions, surfacing buying signals well in advance of formal RFPs. This proactive approach allows teams to engage potential clients earlier in the buying cycle.
What types of organizations can benefit from Pursuit?
Pursuit is tailored for any organization looking to sell to state, local, and educational government entities. This includes GovTech companies, established government contractors, and sales teams focused on the public sector.
Can Pursuit integrate with existing CRM systems?
Yes, Pursuit offers native integrations with popular CRM systems like Salesforce and HubSpot. This enables seamless data flow, reducing the need for manual data entry and ensuring that teams have access to the most accurate information.
How does Pursuit enhance collaboration among teams?
Pursuit facilitates shared intelligence across go-to-market teams, enabling seamless communication and collaboration. With everyone operating on the same data, signals can flow effortlessly from marketing initiatives to sales outreach and customer success efforts.
Threat Watch FAQ
What types of assets does Threat Watch discover and monitor?
Threat Watch automatically discovers and continuously monitors a wide range of external digital assets. This includes all owned domains and subdomains, public IP addresses, SSL certificates, cloud storage instances (e.g., AWS S3 buckets, Azure Blobs), and network infrastructure devices exposed to the internet. The discovery process is agentless and based on passive and active reconnaissance techniques, ensuring comprehensive coverage without requiring internal network access.
How does Threat Watch source its data on compromised credentials and dark web exposures?
The platform aggregates data from a vast array of sources, including continuous crawling of dark web marketplaces, forums, and paste sites; integration with commercial and proprietary breach databases; and monitoring of underground communication channels. This data is then de-duplicated, validated, and correlated with the organization's monitored assets (e.g., corporate email domains) to ensure alerts are relevant and actionable, reducing false positives.
Can Threat Watch integrate with our existing security tools?
Yes, Threat Watch is built with an API-first architecture, enabling robust integration capabilities. It offers out-of-the-box integrations with major SIEM platforms (e.g., Splunk, IBM QRadar, LogRhythm), ticketing systems (e.g., ServiceNow, Jira), and orchestration tools. This allows automated ingestion of Threat Watch intelligence into existing workflows, ensuring alerts are acted upon within established security processes and that data is available for correlation with internal telemetry.
What is the deployment process and does it require internal agents?
Threat Watch is delivered as a cloud-native Software-as-a-Service (SaaS) platform, requiring no software installation or internal deployment of agents. The setup process is typically initiated by defining the organization's digital assets (e.g., root domains, IP ranges) for monitoring. The platform then begins its automated discovery and scanning processes externally, with no impact on internal network performance or bandwidth.
Alternatives
Pursuit Alternatives
Pursuit is an AI-driven sales intelligence platform designed specifically for businesses targeting state, local, and educational (SLED) government entities. By leveraging advanced algorithms, Pursuit helps users identify high-probability sales opportunities and key contacts within a fragmented public sector market, streamlining the complex process of public-sector sales. Users often seek alternatives to Pursuit due to factors such as pricing, specific feature sets, or a need for different platform capabilities. When exploring alternatives, it is essential to consider the comprehensiveness of the data offered, the effectiveness of opportunity detection, and the overall user experience. A robust alternative should equip sales teams with actionable insights while aligning with their unique sales strategies.
Threat Watch Alternatives
Threat Watch is a specialized Business Intelligence platform focused on external attack surface management and cybersecurity exposure. It provides automated, continuous diagnostics of an organization's digital footprint, prioritizing risks from credential leaks to vulnerable internet-facing assets. Organizations may seek alternatives for various operational reasons. Common drivers include budget constraints, the need for specific feature integrations, or a requirement for a platform that aligns with a different internal workflow or existing security stack. The search often centers on finding a tool that matches their unique scale and risk profile. When evaluating alternatives, key criteria should include the scope of attack surface discovery, the depth and sources of dark web and credential monitoring, the automation of risk prioritization, and the platform's ability to deliver actionable intelligence that reduces mean time to remediation. The ideal solution offers comprehensive visibility tailored to the organization's asset landscape.
