aVenture vs Threat Watch
Side-by-side comparison to help you choose the right tool.
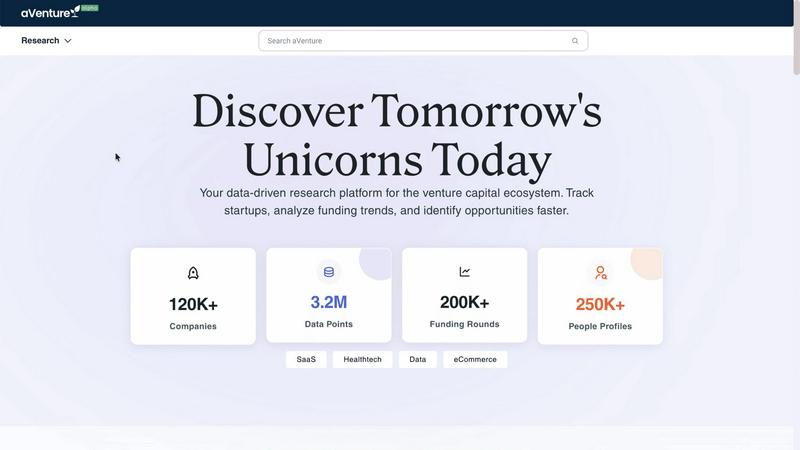
aVenture provides institutional-grade research on over 100,000 private companies and venture capital data.
Last updated: March 1, 2026
Threat Watch
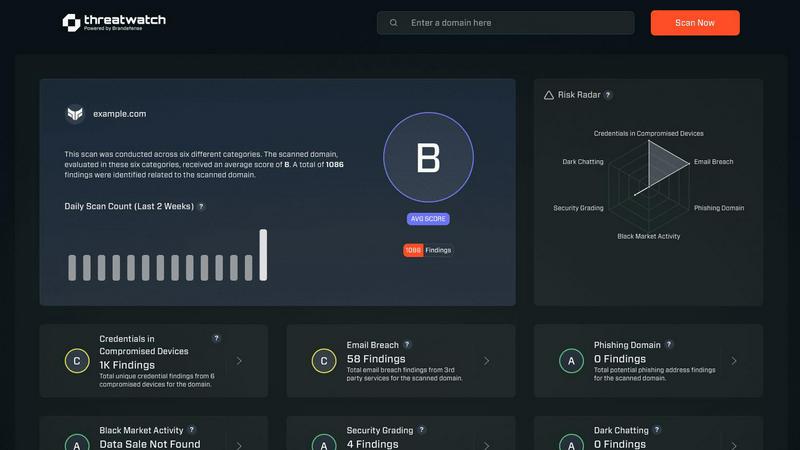
Threat Watch instantly analyzes your cybersecurity posture across credentials, devices, and dark web exposures.
Last updated: March 1, 2026
Visual Comparison
aVenture
Threat Watch
Feature Comparison
aVenture
Institutional-Grade Company Database
The platform maintains a dynamically updated database tracking over 107,109 active venture-backed companies, providing foundational data on funding rounds, valuation trends, and key personnel. Coverage spans 132 countries, ensuring a truly global perspective on private market activity. This database serves as the primary source for all analytical functions, with data integrity ensured through aggregation from more than 1,200 verified sources.
AI-Powered Analyst Engine
aVenture's proprietary AI engine automates the synthesis of complex venture data and news flow. It continuously scans and processes the latest coverage to generate intelligent summaries that highlight company traction, strategic shifts, and potential risks. This feature distills vast amounts of unstructured information into concise, actionable insights, explaining the material impact of new events on a company's position and prospects.
Deep Company Insights & Analytics
Beyond basic tracking, the platform provides granular analysis of ownership structures, cap table evolution, competitive positioning, and detailed funding histories. Users can surface insights into investor syndicates, follow-on investment patterns, and market share dynamics. This depth of analysis is calibrated to meet the due diligence standards of institutional investors and sophisticated corporate development teams.
Comprehensive Market & Trend Intelligence
aVenture aggregates data on 29,779 investors and 211,033 key people, facilitating advanced market mapping and trend analysis. Users can analyze sector-specific investment flows, identify the most active venture capital firms, and track emerging industry themes. The platform contextualizes individual company data within broader market movements, supporting strategic forecasting and opportunity identification.
Threat Watch
Continuous Attack Surface Monitoring
Threat Watch performs non-stop, automated discovery and inventory of all external-facing digital assets linked to an organization, including domains, subdomains, IP addresses, and cloud instances. It employs advanced reconnaissance techniques to map the entire attack surface, ensuring no asset goes unmonitored. This continuous scanning provides a real-time, dynamic view of potential entry points for adversaries, forming the foundational layer for all subsequent security analysis and threat detection processes.
Unified Threat Intelligence Correlation
The platform's core engine aggregates raw data from a multitude of sources, including proprietary scanners, breach databases, phishing feeds, and dark web monitoring. It then applies correlation algorithms and contextual analysis to transform this data into prioritized intelligence. By linking a compromised credential found on the dark web to a vulnerable server in the IT inventory, Threat Watch provides a complete narrative of risk, moving beyond isolated alerts to deliver a comprehensive understanding of interconnected threats.
Automated Exposure Assessment & Prioritization
Threat Watch automatically assesses identified exposures against severity and impact criteria, assigning a risk score to each finding. It utilizes a rules-based prioritization engine that factors in asset criticality, exploit availability, and threat actor activity. This automation eliminates alert fatigue by surfacing only the most critical issues that require immediate intervention, allowing security teams to focus their resources effectively on remediating the vulnerabilities that pose the greatest business risk.
Real-Time Alerting and Integrations
The platform provides configurable, real-time alerting via email, SMS, and integration with popular Security Information and Event Management (SIEM) systems and ticketing platforms like ServiceNow and Jira. This ensures that critical findings are routed directly into existing security workflows and incident response procedures without delay. The API-first design allows for seamless data exchange with other security tools, enabling Threat Watch to function as a central intelligence hub within a broader security architecture.
Use Cases
aVenture
Investment Due Diligence and Deal Sourcing
Investment professionals utilize aVenture to conduct thorough due diligence on target companies, examining complete funding histories, investor backgrounds, and competitive benchmarks. The platform's screening and alerting capabilities enable analysts to systematically source new deal flow by identifying high-growth companies in specific sectors, stages, or geographies that match their investment thesis.
Fundraising Preparation and Investor Targeting
Founders and startup executives leverage the platform to prepare for fundraising rounds. They can benchmark against similar companies, understand prevailing valuation metrics, and identify the most relevant and active investors for their sector and stage. This enables the construction of a targeted, data-backed outreach strategy to secure optimal financing.
Competitive and Market Landscape Analysis
Business development and corporate strategy teams use aVenture to monitor their competitive landscape, tracking rivals' funding events, partnership announcements, and strategic hires. The platform allows for comprehensive market mapping to identify potential partners, acquisition targets, or emerging disruptive threats within a defined market segment.
Limited Partner (LP) Portfolio Monitoring
Limited Partners and fund-of-funds managers employ aVenture to monitor the performance and activity of their venture capital fund investments. They can track the portfolios of their general partner (GP) relationships, analyze the health and progress of underlying portfolio companies, and gain visibility into follow-on funding rounds and exit events.
Threat Watch
Proactive External Risk Management for CISOs
CISOs and risk management leaders utilize Threat Watch to gain a continuous, board-ready overview of the organization's external cyber risk posture. The platform provides quantified metrics and trending data on exposure categories, enabling informed decision-making on security investments and resource allocation. It supports compliance reporting and demonstrates due diligence by providing evidence of proactive monitoring and management of digital risks beyond the corporate firewall.
Accelerated Incident Response and Threat Hunting
Security Operations Center (SOC) analysts and incident responders use Threat Watch to rapidly investigate security alerts and breaches. By providing immediate context—such as whether a compromised employee credential is actively for sale or if a breached server was previously identified as vulnerable—the platform significantly shortens investigation cycles. It serves as a critical tool for proactive threat hunting, allowing teams to search for indicators of compromise (IOCs) related to their specific organization across monitored datasets.
Third-Party and Supply Chain Risk Assessment
Organizations employ Threat Watch to evaluate the external security posture of partners, vendors, and acquisition targets. By monitoring the digital assets associated with third-party entities, security teams can identify if a supplier's exposed credentials or vulnerable systems could serve as a pivot point into their own network. This use case extends the platform's value beyond internal security to managing supply chain and ecosystem risk.
Brand Protection and Phishing Mitigation
Marketing and fraud prevention teams leverage the platform's capabilities to detect phishing campaigns and brand impersonation. Threat Watch continuously scans for fraudulent domains, phishing kits, and malicious infrastructure that mimic the organization's legitimate web properties. Early detection allows for swift takedown requests and proactive customer communication, thereby protecting the brand's reputation and reducing the success rate of social engineering attacks.
Overview
About aVenture
aVenture is an institutional-grade venture intelligence platform engineered to deliver comprehensive, data-driven insights into the global private market. It functions as a centralized data hub, aggregating and synthesizing information from over 1,200 distinct sources to track more than 107,109 active venture-backed companies across 132 countries. The platform's core architecture is built to process over 12.4 million distinct data points, encompassing funding histories, ownership structures, investor portfolios, and competitive landscapes. Its primary value proposition is the transformation of this vast, raw data into actionable intelligence through advanced analytics and a proprietary AI-driven synthesis engine. This AI analyst continuously processes real-time news and coverage to generate concise summaries of company traction, flag potential risks, and elucidate the material impact of new developments. aVenture is designed for a professional user base that includes investment analysts conducting due diligence and market mapping, founders preparing for fundraising rounds, business development teams scouting for partners or acquisition targets, and corporate strategists monitoring competitive threats and emerging opportunities. By providing deep, reliable visibility into the venture ecosystem, aVenture enables precision in deal sourcing, diligence, and strategic outreach.
About Threat Watch
Threat Watch is a sophisticated, unified cybersecurity intelligence and exposure management platform engineered for enterprise IT security teams, Chief Information Security Officers (CISOs), and risk management professionals. It serves as a centralized diagnostic console for an organization's external cyber health, providing continuous, automated surveillance and analysis of its entire digital asset portfolio. The platform's architecture is designed to aggregate, normalize, and correlate disparate security signals from across the clear, deep, and dark web into a single, coherent, and actionable overview. By perpetually mapping and scanning the external attack surface, Threat Watch identifies, validates, and prioritizes critical security exposures across five core categories: compromised credentials, vulnerable internet-facing devices, breached corporate accounts, active phishing infrastructure, and dark web data leaks. This intelligence-driven approach enables organizations to transition from a reactive, incident-response model to a proactive, preventative security posture. The solution delivers real-time insights and automated risk assessments, which dramatically reduces both the Mean Time to Identify (MTTI) and Mean Time to Remediate (MTTR) critical vulnerabilities, thereby systematically hardening an organization's external defenses against evolving cyber threats.
Frequently Asked Questions
aVenture FAQ
What is the source of aVenture's data?
aVenture aggregates its data from a comprehensive network of over 1,200 primary and secondary sources. This includes regulatory filings, news publications, company websites, direct submissions, and partner data feeds. The platform's proprietary data ingestion and normalization systems continuously update and cross-reference this information to ensure accuracy and comprehensiveness across its database of 107,109+ companies.
How does the AI Analyst engine work?
The AI Analyst engine employs natural language processing (NLP) and machine learning models to scan, read, and synthesize vast quantities of unstructured text from news articles, press releases, and financial reports. It identifies key events, extracts relevant metrics, and contextualizes information against the platform's existing company profiles to generate concise summaries on traction, risks, and strategic developments without requiring manual research.
What types of companies and investors are covered?
The platform focuses on venture-backed private companies globally, spanning from early-stage startups to late-stage pre-IPO unicorns. It tracks over 29,779 investors, including venture capital firms, corporate venture arms, angel investors, private equity firms involved in growth equity, and accelerators like Y Combinator. Coverage is strongest in major innovation hubs but extends across 132 countries.
Can I track specific sectors or industries with aVenture?
Yes, aVenture offers advanced filtering and tagging capabilities that allow users to track companies and investment activity within specific sectors such as SaaS, Healthtech, Fintech, Cleantech, and more. Users can create custom alerts, build watchlists, and generate reports based on these industry classifications to monitor trends and opportunities in their areas of interest.
Threat Watch FAQ
What types of assets does Threat Watch discover and monitor?
Threat Watch automatically discovers and continuously monitors a wide range of external digital assets. This includes all owned domains and subdomains, public IP addresses, SSL certificates, cloud storage instances (e.g., AWS S3 buckets, Azure Blobs), and network infrastructure devices exposed to the internet. The discovery process is agentless and based on passive and active reconnaissance techniques, ensuring comprehensive coverage without requiring internal network access.
How does Threat Watch source its data on compromised credentials and dark web exposures?
The platform aggregates data from a vast array of sources, including continuous crawling of dark web marketplaces, forums, and paste sites; integration with commercial and proprietary breach databases; and monitoring of underground communication channels. This data is then de-duplicated, validated, and correlated with the organization's monitored assets (e.g., corporate email domains) to ensure alerts are relevant and actionable, reducing false positives.
Can Threat Watch integrate with our existing security tools?
Yes, Threat Watch is built with an API-first architecture, enabling robust integration capabilities. It offers out-of-the-box integrations with major SIEM platforms (e.g., Splunk, IBM QRadar, LogRhythm), ticketing systems (e.g., ServiceNow, Jira), and orchestration tools. This allows automated ingestion of Threat Watch intelligence into existing workflows, ensuring alerts are acted upon within established security processes and that data is available for correlation with internal telemetry.
What is the deployment process and does it require internal agents?
Threat Watch is delivered as a cloud-native Software-as-a-Service (SaaS) platform, requiring no software installation or internal deployment of agents. The setup process is typically initiated by defining the organization's digital assets (e.g., root domains, IP ranges) for monitoring. The platform then begins its automated discovery and scanning processes externally, with no impact on internal network performance or bandwidth.
Alternatives
aVenture Alternatives
aVenture is an institutional-grade venture intelligence platform within the business intelligence category. It provides AI-powered research and analytics on over 100,000 private companies, synthesizing vast datasets into actionable insights for professional users. Users may explore alternatives for various reasons, including budget constraints, specific feature requirements not covered by the platform, or the need for a different user interface or data integration capability. The search often stems from a need to align tool capabilities with precise operational workflows or cost structures. When evaluating an alternative, key considerations should include the depth and accuracy of the private company database, the sophistication of analytical and AI synthesis tools, the frequency and sources of data updates, and the platform's ability to serve specific user roles such as investors, analysts, or corporate development teams.
Threat Watch Alternatives
Threat Watch is a specialized Business Intelligence platform focused on external attack surface management and cybersecurity exposure. It provides automated, continuous diagnostics of an organization's digital footprint, prioritizing risks from credential leaks to vulnerable internet-facing assets. Organizations may seek alternatives for various operational reasons. Common drivers include budget constraints, the need for specific feature integrations, or a requirement for a platform that aligns with a different internal workflow or existing security stack. The search often centers on finding a tool that matches their unique scale and risk profile. When evaluating alternatives, key criteria should include the scope of attack surface discovery, the depth and sources of dark web and credential monitoring, the automation of risk prioritization, and the platform's ability to deliver actionable intelligence that reduces mean time to remediation. The ideal solution offers comprehensive visibility tailored to the organization's asset landscape.